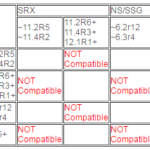
This article describes the issue of the SRX device, which has configured VPN with SHA2 in the IPsec proposal, being unable to decrypt the encrypted traffic; even though it has established the VPN tunnel. Junos and SSG have two generations of SHA2-256 algorithms; the first one uses the 96 bit-length data field and the second one uses the 128 bit-length data field. Due to … [Read more...]
Cleaning the SRX Filesystem to maximize Available Disk Space
Sometimes the "request system storage cleanup" command will still not free enough disk space. This article will show an administrator how to maximize the free space on SRX. The SRX does not have enough free space to finish a task, be it IDP update, or Junos upgrade. Even after running "request system storage cleanup" the SRX admin notices that there is not enough free space. … [Read more...]
High RE CPU utilization seen on awk process after NSM upgrade
When upgrading NSM from a version prior to 2011.4s2 to a newer version, high CPU utilization might be observed on the SRX device through the awk process. This article explains the event and describes how to change a configuration option to resolve the problem. Beginning with NSM 2011.4s2, a new feature was added into NSM to detect configuration changes made outside NSM (such … [Read more...]
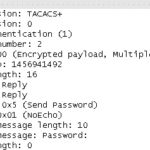
J-Web login does not support TACACS+ or TACPLUS Authentication
This article describes the issue of TACACS+ or TACPLUS authentication not being supported by J-Web login. When TACPLUS configured in SRX, SSH can login without any issues; but J-Web can login at times, however it also fails at times. In the case of TACPLUS login failure with J-Web, the following error message is generated in the message log: checklogin[81632]: warning: … [Read more...]
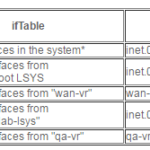
Polling routing-instances and logical-systems with SNMP v1 or SNMP v2c.
This article describes how you can control the scope of polled data by specifying the name of logical-system and/or routing-instance in the community string. It is applicable for SNMP v1 or SNMP v2c. Note: Logical-systems are supported only on High-End SRX Series. The rest is applicable both for High-End SRX and for Branch SRX Series. When monitoring an SRX device with … [Read more...]
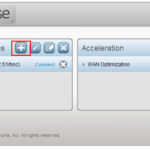
Using Junos Pulse to connect Dynamic VPN client to SRX
Using Junos Pulse to connect Dynamic VPN client to SRX Steps to connect Dynamic VPN client to SRX using Junos Pulse Note: This article will be updated regularly with new findings. Please check back for updates or click 'subscribe' at the top of the article to get notifications. Instructions for the SRX and client are as follows: SRX Follow the steps in the Dynamic … [Read more...]
Best practice guide for IDP deployment on branch SRX devices
This article provides the best practice guide that can used, when IDP, UTM, NSM, AppSecure, and other features are simultaneously running on Branch SRX devices that have a memory of 1GB. Advanced security software memory usage is growing from release to release, due to increased functionality and use of combined features, such as IDP, UTM (anti-virus, anti-spam, web … [Read more...]
IP Monitoring on SRX-Series gateways
This article provides information on how to configure IP monitoring on SRX-Series gateways. IP Monitoring is supported on all high end devices. IP Monitoring is supported on all branch devices running 11.2 or later. Introduction: This feature is used to track the coverage of a set of configured IP addresses. It impacts the failover of redundancy groups based … [Read more...]
Control link SFP not shown in show chassis hardware
This article explains why the control link SFP is not shown in show chassis hardware, when SRX1400 is in a cluster. When the show chassiss hardware command is executed, the output will be: SRX1400 not in cluster, sfp 10 and 11 on fpc 0 are shown. root> show chassis hardware Hardware inventory: Item Version Part number Serial number … [Read more...]
Domain names are not being resolved when used in security polices
This article describes an issue that may occur when using domain names in security policies on the SRX. It explains the possible cause of this issue and shows a simple workaround. When defining security policies on the SRX, address-book entries are used to specify source-address and destination-address fields of the policy. One of the possible options to define a value of … [Read more...]