CCNP Route FAQ: IP Addressing Q1. Identify one criterion to help determine a subnet mask for classful addressing when designing a network-addressing scheme. Answer: Questions to ask include the following: How many networks are there in the network? How many hosts are there on the largest subnet? Q2. Which command is used to forward broadcast traffic across a … [Read more...]
CCNP Security FAQ: Profiling
CCNP Security FAQ: Profiling Q1. True or False? The profiling service is enabled by default on ISE policy service nodes. a. True b. False Answer: A. Profiler is enabled by default on all policy service nodes and standalone nodes. However, not a single probe is enabled by default in ISE 1.2. Q2. Name three ways in which an endpoint profile can be used in an authorization … [Read more...]
CCNP Security FAQ: Deploying Guest Services
CCNP Security FAQ: Deploying Guest Services. Figure: WebAuth process flow. Q1. ISE Guest Services use which of the following approaches to authenticate a user? a. Badge b. WebAuth c. TACACS+ d. SSH Answer: B. When a guest connects to the network, they are given a web-redirect authorization policy. This web redirect will intercept any attempts to browse the Internet, … [Read more...]
CCNP Security FAQ: Web Authentication
CCNP Security FAQ: Web Authentication Figure: Web authentication. Q1. Before a Cisco switch will generate a self-signed certificate, which configuration is required? a. The internal CA must be enabled. b. An IPv6 address. c. A Cisco switch cannot generate a self-signed certificate. d. A domain name. Answer: D. The Cisco switch will need the https server enabled to … [Read more...]
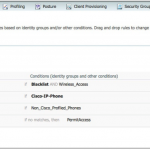
CCNP Security FAQ: Authorization Policies
CCNP Security FAQ: Authorization Policies Figure: Default authorization policy Q1. What is an authorization profile? a. An authorization profile is a rule in the policy table that is formatted like “IF condition THEN result.” b. An authorization profile is created to determine which identity store to validate the credentials with. c. An authorization profile is a … [Read more...]
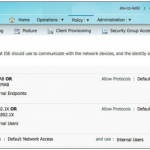
CCNP Security FAQ: Authentication Policies
CCNP Security FAQ: Authentication Policies Figure: Default authentication policy. Q1. Which of the following is required to perform MAB from a Cisco network device? a. The RADIUS packet must have the service-type set to login and the calledstation-id populated with the MAC address of the endpoint. b. The RADIUS packet must have the service-type set to Call-Check and the … [Read more...]
CCNP Security FAQ: Initial Configuration of Cisco ISE
CCNP Security FAQ: Initial Configuration of Cisco ISE Q1. Which rights and permissions are required for the account used to join Cisco ISE to the Active Directory domain? a. Search Active Directory, Remove workstation from domain, Change passwords b. Write to Active Directory, Add workstation to organizational unit, Read properties of computer objects c. Search Active … [Read more...]
CCNP Security FAQ: A Guided Tour of the Cisco ISE Graphical User Interface
CCNP Security FAQ: A Guided Tour of the Cisco ISE Graphical User Interface Figure: Initial ISE administrative GUI login. Q1. Which is true of the Cisco ISE GUI? a. Requires a separate application to access it b. Uses a “standard,” Adobe Flash-capable web-browser c. Does not exist—ISE is only configurable via command-line interface (CLI) d. Requires Cisco Network … [Read more...]
CCNP Security FAQ: Cisco Identity Services Engine Architecture
CCNP Security FAQ: Cisco Identity Services Engine Architecture Figure: Single-node/standalone ISE configuration. Q1. Cisco Identity Services Engine (ISE) is which of the following? a. A switch that provides authenticated access to the network b. A network management platform c. A network security and policy platform d. A unified computing system that incorporates … [Read more...]
CCNP Security FAQ: Introduction to AAA Advanced Concepts
Q1. A RADIUS change of authorization enables an authentication server to do which of the following? a. Escalate an administrative user’s access level within the server’s administration portal b. Grant context appropriate network access after initial access has previously been granted c. Gain root-level access of all network devices d. Take over the world Answer: B. A … [Read more...]