CCNP Security FAQ: Troubleshooting Tools Figure: Live sessions Q1. Which ISE diagnostic tool can be used to find misconfigurations in a Cisco NAD? a. TCP Dump b. Live Sessions Log c. RADIUS Authentication Troubleshooting Tool d. Evaluate Configuration Validator Answer: D. The Evaluate Configuration Validator tool compares a switch configuration to a “template” … [Read more...]
CCNP Security FAQ: Non-802.1X Authentications
CCNP Security FAQ: Non-802.1X Authentications Figure:Web authentication. Q1. True or False? To allow endpoints without configured supplicants to connect to a network where IEEE 802.1X has been enabled, the administrator must disable 802.1X on the endpoints’ switch port. a. True b. False Answer: B. The available options for nonauthenticating endpoints are MAC Authentication … [Read more...]
CCNP Security FAQ: Deploying Safety
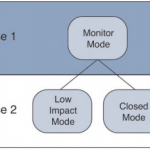
CCNP Security FAQ: Deploying Safety Figure: Phased deployments. Q1. What is Monitor Mode? a. Using the authentication open interface configuration command on 802.1X enabled interfaces b. A setting in ISE to record actions but not take them c. A method for identifying which device would have failed authentication and correcting the root cause prior to it taking … [Read more...]
CCNP Security FAQ: Posture Assessment
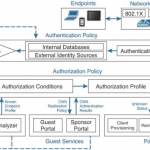
CCNP Security FAQ: Posture Assessment Figure: ISE authentication and authorization flow. Q1. The Posture Service is comprised of which of the following functional components? (Select three.) a. Profiling b. Client provisioning c. Authorization policy d. Mobile device managers e. Access lists f. Guest Services g. Posture Policy Answer: B, C, G. The three major … [Read more...]
CCNP Security FAQ: Identity Management
CCNP Security FAQ: Identity Management Figure ISE identity source sequence configuration Q1. What are two types of identities used in Cisco Identity Service Engine? a. SSID b. MAC address c. Username d. IP address Answer: B, C. An identity is a representation of who a user or device is. Cisco ISE uses an endpoint’s MAC address to uniquely identify that endpoint. A … [Read more...]
CCNP Security FAQ: TrustSec and MACSec
CCNP Security FAQ: TrustSec and MACSec Figure: MACSec Layer-2 hop-by-hop encryption. Q1. What is a security group tag? a. A luggage tag applied by TSA workers at airports to flag bags as they enter security checkpoints b. An internal assignment used in ISE to represent a local copy of an Active Directory group c. A 16-bit value that represents the context of a user … [Read more...]
CCNP Security FAQ: Bring Your Own Device
CCNP Security FAQ: Bring Your Own Device Figure: BYOD timeline. Q1. What is the process of onboarding as it relates to BYOD? a. It’s a form of torture used in military interrogations. b. It prepares an endpoint for network access with supplicant configuration, and possibly even certificate provisioning. c. It’s the process in which an IT department will prestage an … [Read more...]
CCNP Route FAQ: Routing over Branch Internet Connections
CCNP Route FAQ: Routing over Branch Internet Connections Figure: Example Small, Medium, and Large Branch Designs Q1. Router R1 sits at an Enterprise branch office, using the Internet for its only connectivity back to the rest of the Enterprise. Which of the following is not a benefit of using an IPsec tunnel for packets sent through the Internet, between R1 and the rest … [Read more...]
CCNP Route FAQ: IPv4 and IPv6 Coexistence
CCNP Route FAQ: IPv4 and IPv6 Coexistence Figure: Simple IPv4 Enterprise Network Q1. An enterprise has plans to start adding IPv6 support. For the first year, the IPv6 will be in small pockets spread around the existing large IPv4 network, with occasional IPv6 traffic while applications teams test IPv6-enabled servers and applications. Which of the following tools would … [Read more...]
CCNP Route FAQ: IPv6 Routing Protocols and Redistribution
CCNP Route FAQ: IPv6 Routing Protocols and Redistribution Figure: Sample Internetwork for IPv6 Routing Protocol Configuration Q1. Which of the following features work the same in both RIP-2 and RIPng? (Choose three.) a. Distance Vector Logic b. Uses UDP c. Uses RIP-specific authentication d. Maximum useful metric of 15 e. Automatic route summarization Answer: A, B, … [Read more...]