CCNP Secure FAQ Implementing and Configuring Advanced 802.1X Q1. To provide per-user services, such as downloadable ACLs, which of the following must be deployed? (Select all that apply.) A. User authentication B. Machine authentication C. Combination of user and machine authentication D. One-time passwords E. All of these answers are correct. Answer: A and C Q2. In … [Read more...]
CCNP Secure FAQ: Deploying Scalable Authentication in Site-to-Site IPsec VPNs
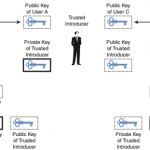
CCNP Secure FAQ: Deploying Scalable Authentication in Site-to-Site IPsec VPNs Q1. What is the one central trusted introducer called? a. Identity certificate b. RSA algorithm c. Certificate authority d. X.500 distinguished name e. None of these answers are correct. Answer: C Figure: Showing Where the Trusted Introducer Is (User B) Q2. A list of all certificates … [Read more...]
CCNP Secure FAQ Implementing and Configuring Basic 802.1X
CCNP Secure FAQ Implementing and Configuring Basic 802.1X Q1. Which of the following three components comprise Cisco 802.1X authentication? A. Cisco IOS Software 802.1X authenticator B. Cisco Secure ACS 4.2 Server C. Cisco Secure Services Client wired 802.1X supplicant D. Cisco MARS E. Microsoft SQL Server Answer: A, B, and C Q2. Which 802.1X component is also known as … [Read more...]
CCNP Secure FAQ: Deploying DMVPNs
CCNP Secure FAQ: Deploying DMVPNs Q1. Which mechanism provides a scalable multiprotocol tunneling framework with optional dynamic routing? a. NHRP b. IPsec c. GRE d. 802.1X e. None of these answers are correct. Answer: C Q2. Which mechanism provides dynamic mutual discovery of spoke devices? a. GRE b. IKE c. NHRP d. DHCP e. Expired Certificate … [Read more...]
CCNP Secure FAQ: Deploying High Availability in Tunnel-Based IPsec VPNs
CCNP Secure FAQ: Deploying High Availability in Tunnel-Based IPsec VPNs Q1. What can be used to mitigate device failure? a. Single ISP transport networks b. Multiple ISP transport networks c. Multiple devices at a site d. Redundant interfaces on a VPN device Answer: C Q2. What can be done to provide high availability when the cost of redundant devices cannot be … [Read more...]
CCNP Secure FAQ Configuring and Implementing Switched Data Plane Security Solutions
CCNP Secure FAQ Configuring and Implementing Switched Data Plane Security Solutions Q1. What is the default inactivity expire time period on a Cisco Catalyst switch CAM table? A. 1 minute B. 5 minutes C. 10 minutes D. 50 minutes Answer: B Q2. Which of the following attack types describes when an attacker tries to take over the root bridge functionality on a network? A. … [Read more...]
CCNP Secure FAQ: Deploying Remote Access Solutions Using EZVPN5
CCNP Secure FAQ: Deploying Remote Access Solutions Using EZVPN5 Q1. What enables Cisco Integrated Services Routers to act as VPN gateways? a. Cisco EZVPN Remote b. PKI c. Cisco EZVPN Server d. None of these answers are correct. Answer: C Q2. What can the EZVPN server use to create cryptographic tunnel contexts? (Select all that apply.) a. VTI b. IPsec c. Crypto … [Read more...]
CCNP Secure FAQ Network Foundation Protection (NFP) Overview
CCNP Secure FAQ Network Foundation Protection (NFP) Overview Q1. Which of the following is the functional device plane that provides the ability to allow network administrators to connect to the device to execute configuration commands? A. Data plane B. Control plane C. Management plane D. Router plane Answer: C Q2. Which functional device plane is responsible for … [Read more...]
CCNP Secure FAQ: Deploying Remote Access Solutions Using SSL VPNs
CCNP Secure FAQ: Deploying Remote Access Solutions Using SSL VPNs Q1. Which type of SSL VPN architecture supports any IP application without application modification? a. Full tunneling b. Split tunneling c. Clientless tunneling d. None of these answers are correct. Answer: A Figure: Full Tunneling Scenario Q2. Which type of VPN architecture allows remote users URL … [Read more...]
CCNP Secure FAQ: Deploying GET VPNs
CCNP Secure FAQ: Deploying GET VPNs Q1. GET VPNs use which feature to provide large-scale transmission protection that uses the existing routing infrastructure? (Select all that apply.) a. Tunnel-free b. X.500 c. Connectionless d. ISAKMP e. Encrypted Answer: A and C Q2. GET VPNs use a concept of which of the following to provide transmission protection? (Select all … [Read more...]