In this article, we'll sum up some of the ways you can avoid hackers and cheaters in PUBG Mobile to have a healthy and fun gaming experience. As everybody knows, hacks and cheats are an ever-present issue that has plagued the gaming scene pretty much since the dawn of video games. Most games, be they offline single-player or competitive multiplayer, are vulnerable to cheats, … [Read more...]
PUBG Guns Guide, Which Are The Best PUBG Guns?
PUBG is among the most played Esports recently. Go grab your favorite PUBG guns and start doing the most exciting thing in the game, killing. One of the most diverse features in the game is PUBG guns. PUBG is a popular Esports which requires the element of competition and survival to emerge on top of everyone. The genre of the game is battle royale. You either need to kill … [Read more...]
CCNA Security Lab: Exploring Encryption Methods
CCNA Security Lab: Exploring Encryption Methods Topology Objectives Part 1: (Optional) Build the Network and Configure the PCs Connect the PCs and configure IP addresses. Part 2: Decipher a Pre-encrypted Message Using the Vigenere Cipher Given an encrypted message, a cipher key, and the Vigenere cipher square, decipher the message. Part 3: Create a … [Read more...]
CCNP Route FAQ: Internal BGP and BGP Route Filtering
CCNP Route FAQ: Internal BGP and BGP Route Filtering Q1. R1 in ASN 1 with loopback1 address 1.1.1.1 needs to be configured with an iBGP connection to R2 with loopback2 IP address 2.2.2.2. The connection should use the loopbacks. Which of the following commands is required on R1? a. neighbor 1.1.1.1 remote-as 1 b. neighbor 2.2.2.2 remote-as 2 c. neighbor 2.2.2.2 … [Read more...]
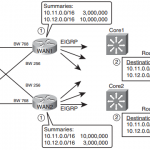
CCNP Route FAQ: EIGRP Route Summarization and Filtering
CCNP Route FAQ: EIGRP Route Summarization and Filtering Figure: Choosing Locations for Route Summarization Q1. Router R1 has been configured for EIGRP. The configuration also includes an ACL with one line–access-list 1 permit 10.100.32.0 0.0.15.255–and the EIGRP configuration includes the distribute-list 1 in command. Which of the following routes could not be displayed … [Read more...]
Network Security Basics and the Need for Network Security
Network Security Basics and the Need for Network Security In this section, we examine some of the key principles involved in creating a secure network. We establish building blocks that will be used in formulating an effective security policy. The principles are as follows: Open networks and knowledgeable attackers with sophisticated attack methods create the requirement … [Read more...]
CCNP Switch FAQ: Switch Operation
CCNP Switch FAQ: Switch Operation Q1. Which of the following devices performs transparent bridging? a. Ethernet hub b. Layer 2 switch c. Layer 3 switch d. Router Answer: B Figure: A Comparison of Transparent Bridges and Switches Q2. When a PC is connected to a Layer 2 switch port, how far does the collision domain spread? a. No collision domain exists. b. One … [Read more...]
CCNP Security FAQ : Configuring Access
CCNP Security FAQ : Configuring Access Q1. Which of the following are constraints when configuring policy NAT? A. A global address can be used concurrently for NAT and PAT. B. An access list must be used only twice with the nat command. C. Access lists for policy NAT cannot contain deny statements. D. An access list must be used only once with the nat command Answer: C, … [Read more...]
CCNA RSE Lab: 6.2.2.5 Configuring VLANs and Trunking
CCNA RSE Lab: 6.2.2.5 Configuring VLANs and Trunking 6.2.2.5 lab - configuring vlans and trunking answers Topology Addressing Table Device Interface IP Address Subnet Mask Default Gateway S1 VLAN 1 192.168.1.11 255.255.255.0 N/A S2 VLAN 1 192.168.1.12 255.255.255.0 N/A PC-A NIC 192.168.1 0.3 255.255.255.0 192.168.1 … [Read more...]
CCNA RSE Lab: 3.2.1.9 Configuring Basic RIPv2
CCNA RSE Lab: 3.2.1.9 Configuring Basic RIPv2 CCNA 2 Lab 3.2.1.9 lab - configuring basic ripv2 packet tracer Answers Topology Addressing Table Objectives Part 1: Build the Network and Configure Basic Device Settings Part 2: Configure and Verify RIPv2 Routing Configure RIPv2 on the routers and verify that it is running. Configure a passive … [Read more...]