CCNP Switch: Switch Configuration
Switch Management
Managing a Catalyst switch can be broken up into several topics. A switch runs an operating system, which provides a user interface and controls all processes that are used to forward packets. The following sections address all these topics.
Operating Systems
You can configure Cisco Catalyst switch devices to support many different requirements and features. When a PC is connected to the serial console port, configuration generally is done with a terminal emulator application on the PC. You can perform further configurations through a Telnet session across the LAN or through a web-based interface. These topics are covered in later sections.
Catalyst switches support one of two operating systems, each with a different type of user interface for configuration:
- Cisco IOS Software—The user interface is identical to that of Cisco routers, having an EXEC mode for session and monitoring commands, and a hierarchical configuration mode for switch configuration commands.
Cisco IOS Software is supported on all current Catalyst platforms, such as the 2970, 3750, 4500 (with Supervisors III and above), and 6500 (with Supervisor II and MSFC “Supervisor IOS,” also known as “native” code, and Supervisor 720). This operating system can support Layer 2–only switching or Layer 2and Layer 3 operation, depending on the software license. - Catalyst OS (CatOS or COS, also called XDI)—This user interface allows session and monitoring commands to be intermingled with set-based (using the set and clear commands) configuration commands. CatOS is supported on legacy switch families, such as the Catalyst 4000 (Supervisor I or II), Catalyst 5000, Catalyst 5500, and Catalyst 6500 (any Supervisor module, known as “hybrid” code). This operating system can support only Layer 2 switching.
Cisco Field Manual: Catalyst Switch Configuration, by David Hucaby and Steve McQuerry, Cisco Press, ISBN 1-58705-043-9
Comparison of the Cisco Catalyst and Cisco IOS Operating Systems for the Cisco Catalyst 6500 Series Switch, at http://www.cisco.com/en/US/products/hw/switches/ps708/ products_white_paper09186a00800c8441.shtml
Generally, you are provided with an interface where you can issue commands, such as show, to display many different types of information about the switch, its configuration, and dynamic operation. This is called user EXEC mode. Users are given access to various commands, according to their privilege level, ranging from Level 1 through Level 15. By default, a user is given Level 1. To make any configuration changes, a user must enter a higher level, such as Level 15, through the enable command.
When in the privileged EXEC or enable mode, you can make configuration changes using th config command. Configuration is performed in layers, starting with the global configuration. Each time you select a specific item to configure in global configuration mode, you are moved into that respective configuration mode.
The switch prompt changes to give you a clue about your current mode. For example, normal or user EXEC mode generally is shown with the name of the switch followed by a greater-than (>) character. Privileged EXEC (enable) mode replaces the > with a hash or pound sign (#). Global configuration is shown as the switch name followed by (config). If you select an interface to configure, you enter interface configuration mode, signified by (config-if).
Basically, if you are familiar with router EXEC and configuration commands and the IOS user interface, you will be comfortable working with the Catalyst IOS Software.
Identifying the Switch
All switches come from the factory with a default configuration and a default system name or prompt. You can change this name so that each switch in a campus network has a unique identity. This option is useful when you are using Telnet to move from switch to switch in a network. To change the host or system name, enter the following command in configuration mode:
Switch(config)# hostname hostname
The host name is a string of 1 to 255 alphanumeric characters. As soon as this command is executed, the system prompt changes to reflect the new host name.
Passwords and User Access
Normally, a network device should be configured to secure it from unauthorized access. Administrative users can connect to Catalyst switches through an asynchronous serial console port, Telnet sessions, rlogin (remote login), and SSH (secure shell). Catalyst switches offer a simple form of security by setting passwords to restrict who can log in to the user interface. Two levels of user access are available: regular login, or user EXEC mode, and enable login, or privileged EXEC mode. User EXEC mode is the first level of access, which gives access to the basic user interface through any line or the console port. Privileged EXEC mode requires a second password and gives access to set or change switch operating parameters or configurations.
Cisco offers various methods for providing device security and user authentication. Many of these methods are more secure and robust than using the login passwords. Chapter 17, “Securing Switch Access,” describes these features in greater detail. To set the login passwords for user EXEC mode, enter the following commands in global
configuration mode:
Switch(config)# line con 0 Switch(config-line)# password password Switch(config-line)# login Switch(config)# line vty 0 1 5 Switch(config-line)# password password Switch(config-line)# login Switch(config)# enable secret enable-password
Here, the user EXEC mode password is set on the console (line con 0) and on all the virtual terminal (line vty 0 15) lines used for Telnet access. The enable mode password (enable secret), which automatically is encrypted when set, is a global value for all users. The user EXEC password is a string of 1 to 80 alphanumeric characters. The enable secret password is a string of 1 to 25
alphanumeric characters. All passwords are case sensitive.
You can change the passwords by reconfiguring the passwords with different strings. To completely remove a password, use the no password or no enable secret command in the appropriate line-configuration mode.
Password Recovery
After the EXEC and enable passwords are configured, there is always a chance that you could forget them. You also might inherit a switch that has its passwords set to unknown values. In this case, you must take the switch through a password-recovery procedure. The procedure varies among the different Catalyst switch families. Refer to the following documents:
- Catalyst 2970 and 3750—http://www.cisco.com/warp/public/474/pswdrec_2900xl.html
- Catalyst 4000 and 4500 (Supervisor III and above)—http://www.cisco.com/warp/public/ 474/ pswdrec_cat4000_supiii_21229.html
- Catalyst 6500 (Supervisor IOS)—http://www.cisco.com/warp/public/474/
pswdrec_6000IOS.html
For a complete list of password-recovery procedures for any model of Cisco equipment, refer to the handy Password Recovery Procedures technical tip at http://www.cisco.com/warp/public/474/.
TIP Although password recovery is not covered explicitly in the BCMSN course (nor is likely in the CCNP BCMSN exam), you should be aware of the concepts needed to regain access to a switch.
Remote Access
By default, the switch allows user access only via the console port. To use Telnet to access a switch from within the campus network, to use ping to test a switch’s reachability, or to monitor a switch by SNMP, you must configure for remote access.
Even if a switch operates at Layer 2, the switch supervisor processor must maintain an IP stack at Layer 3 for administrative purposes. An IP address and subnet mask then can be assigned to the switch so that remote communications with the switch supervisor are possible.
By default, all ports on a switch are assigned to the same virtual LAN (VLAN) or broadcast domain. The switch supervisor and its IP stack must be assigned to a VLAN before remote Telnet and ping sessions will be supported. VLANs are discussed further in Chapter 6, “VLANs and Trunks.”
You can assign an IP address to the management VLAN (default is VLAN 1) with the following commands in global configuration mode:
Switch(config)# interface vlan vlan-id Switch(config-if)# ip address ip-address netmask Switch(config-if)# ip default- gateway ip-address Switch(config-if)# no shutdown
As demonstrated by the preceding command syntax, an IP address and subnet mask are assigned to the VLAN “interface,” which is really the switch supervisor’s IP stack listening on VLAN number vlan-id. Any VLAN number can be used, as long as the VLAN has been defined and is active (in use on a physical switch interface).
To send packets off that local VLAN subnet, a default gateway IP address also must be assigned. This default gateway has nothing to do with processing packets that are passed through the switch; the default gateway is used only to forward traffic between a user and the switch supervisor for management purposes. (This concept can be expanded greatly on a Layer 3 switch, which can perform its own “routing” functions and can use dynamic routing protocols.) Interswitch Communication: Cisco Discovery Protocol
Because switch devices usually are interconnected, management is simplified if the switches can communicate on some level to become aware of each other. Cisco has implemented protocols on its devices so that neighboring Cisco equipment can be found and identified.
Cisco uses a proprietary protocol on both switches and routers to discover neighboring devices. You can enable the Cisco Discovery Protocol (CDP) on interfaces to periodically advertise the existence of a device and exchange basic information with directly connected neighbors. The information exchanged in CDP messages includes the device type, software version, links between devices, and number of ports within each device.
By default, CDP runs on each port of a Catalyst switch, and CDP advertisements occur every 60 seconds. CDP communication occurs at the data link layer so that it is independent of any network layer protocol that might be running on a network segment. This means that CDP can be sent and received using only Layer 2 functionality. CDP frames are sent as multicasts, using a destination MAC address of 01:00:0c:cc:cc:cc.
Cisco Catalyst switches regard the CDP address as a special address designating a multicast frame that should not be forwarded. Instead, CDP multicast frames are redirected to the switch’s management port and are processed by the switch supervisor alone. Cisco switches become aware only of other directly connected Cisco devices.
CDP is enabled by default on all switch interfaces. To manually enable or disable CDP on an interface, use the following interface-configuration command:
Switch(config-if)# [ no] cdp enable
If a switch port connects to a non-Cisco device or to a network outside your administrative control, consider disabling CDP on that port. Add the no keyword to disable CDP.
Switch File Management
A Catalyst switch uses several types of files while it is operating. To manage a switch, you should understand what type of file is used for what purpose, how to move these files, and how to upgrade them.
The following files typically are used in a Catalyst switch:
- IOS image files—The software or code that the switch CPU executes. Image files are compiled and tailored for specific switch hardware models.
- Configuration files—Text files containing all configuration commands needed to operate a switch in a network.
All Catalyst files can be stored in various file systems so that they can be accessed and used by the switch hardware. Files also can be stored in file systems external to the switch, either as backup copies or as downloadable upgrades.
The typical file systems available to a Catalyst switch are as follows:
- Flash memory—Nonvolatile memory present in the switch; files stored here remain intact even after a power cycle.
- Network servers—Systems apart from the switch that are connected to the network and provide TFTP, FTP, or remote copy program (rcp) file-transfer services.
- NVRAM—Nonvolatile memory that contains the switch configuration used during bootup. On many switches, the NVRAM file system actually is emulated in Flash memory.
- RAM—Volatile memory available to the switch for a variety of purposes. The switch configuration used during runtime and altered by configuration commands is stored here.
OS Image Files
The Catalyst IOS Software is packaged as an IOS image file, just as it is for routers. IOS image files are stored in the Flash memory on a switch. Only one image file can be executed while the switch is running, but more than one image file can be stored on the switch. Switches such as the Catalyst 2970 and 3750 have one Flash area where images are stored. This is always named flash:. Larger, more modular switches can have several Flash file systems. For example, a Catalyst 4500 has one named cat4000_flash: that contains the VLAN database file and another called bootflash: that contains the IOS image and bootstrap image files. Flash memory also can be present in the form of a PCMCIA card, so stored files can be swapped out by replacing the Flash card. These cards are named slot0:, slot1:, and so on.
You can copy IOS image files from one file system to another or to an external location. This allows an image file to be backed up in case of a switch failure. Image files also can be copied into the switch Flash file system so that the software version can be upgraded.
Filename Conventions
IOS image files are named according to a predefined format. The filenames follow this basic template:
mmmmm-fffff-mm.vvvv.bin
- mmmmm represents the Catalyst switch model (for example, c3750 corresponds to Catalyst 3750, cat4000 to Catalyst 4000 or 4500, c6k222 to Catalyst 6500 Supervisor II, and s72033 to Catalyst 6500 Supervisor 720).
- fffffrepresents the feature sets included in the image—generally, i followed by anything denotes an IP feature set, s is the IP “Plus,” k denotes a cryptographic feature set (Data Encryption Standard [DES] or 3DES), j is the enterprise set, p is for service providers, and d is the desktop (IP, IPX, AppleTalk, DECnet) feature set.
- mm denotes the file format: The first letter is m if the image runs in RAM, and the second letter is z if the image is Zip compressed.
- vvvv represents the IOS version, in the format vvv-mmm.bbb; the major release (vvv) is given first and followed by a dash; then the maintenance release (mmm) is given and followed by a period. The build level (bbb) is given using one or more letters and a number. The first letter denotes the type of build: E means an early deployment of features. The next letter is the interim build level, where A means the first build, and so on. The number following denotes the number of times the interim build has been released incrementally. Therefore, 122-20.EWA means version 12.2(20)EWA, or early deployment build WA of the 12.2(20) code.
- bin flags the image file as a binary executable (not readable text).
Configuration Files
The switch configuration is a file containing all the commands needed to configure each switch feature and function. Here are three of the most common configuration files:
- startup-config—When a switch first boots up, the startup-config file is read, parsed, and executed. The startup-config is stored in NVRAM (actually, the nvram: file system), so it survives power failures.
- running-config—While a switch is running, this contains a copy of the current state of every command in use. This file is dynamic, so it is updated with each configuration command entered.
The running-config contents are volatile, causing all commands in it to be lost during a power failure or a switch reload. (To preserve the running-config, it must be copied into the startup-config before the next switch reload.) - vlan.dat—As VLANs are defined or changed, their configurations are entered into the VLAN database file, vlan.dat. This file is updated as you make configuration changes to the VLAN database on a switch and as any VLAN Trunking Protocol (VTP) updates occur. The VLAN database (vlan.dat) is stored in Flash memory (or the const_nvram: filesystem on a Catalyst 6500). The contents of the VLAN database are preserved across a power failure or reload.
Other Catalyst Switch Files
You can find several other files stored in the file systems on a Catalyst switch. Most of the time, you will not need to do anything with them. They are mentioned here for your understanding and in case you need to access the information they contain. These files can include the following:
- system_env_vars—A text file containing system variables such as the MAC address, model number, serial number, and various module information. This file is consulted to get the system information displayed by the show version command.
- crashinfo—A file or directory containing text output from previous switch crashes. This normally is stored and accessed as flash:crashinfo (a file) or crashinfo: (a directory).
Moving Catalyst Switch Files
A switch can copy files to and from various locations, including those in Table 4-2.
Table 4-2 Locations of Catalyst Switch Files
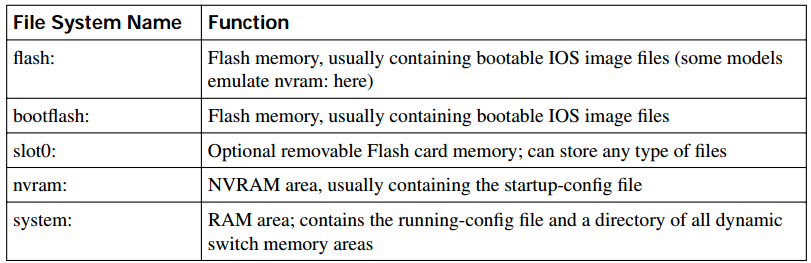
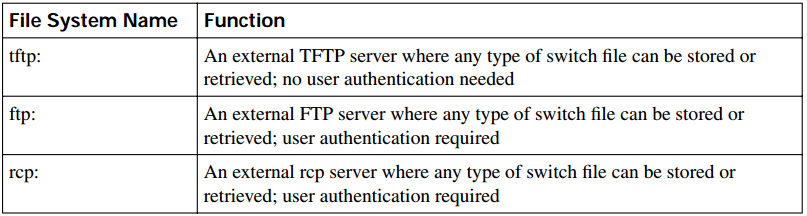
Cisco IOS Software allows you to navigate and manipulate the Flash file system in much the same way other operating systems, such as UNIX and DOS, do. In Flash memory, you can find plaintext files, binary executable files, and directories. You are free to “move” up and down into directories. You also can copy, rename, or delete files.
In the EXEC mode, you always are positioned in the “root” directory, flash:, by default. To perform a function in the Flash file system, use one of the following commands:
- dir [flash:[directory]]—Shows a list of all files in the current Flash directory or the directory given.
- cd flash:directory—Changes the directory to the directory given.
- cd ..—Changes the directory one level up.
- cd—Changes the directory to the home or root Flash directory.
- copy flash:[filename] tftp:—Copies the file filename from Flash to a TFTP server. The server address and destination filename are prompted.
- copy tftp: flash:[filename]—Copies a file from the TFTP server into Flash memory. The TFTP server address and any unresolved filenames are prompted.
- delete flash:filename—The file filename is deleted from Flash memory.
- erase flash:—All files in Flash memory are erased in one command.
- format flash:—The Flash file system is reformatted, destroying all existing files. Formatting is appropriate when the Flash memory has been corrupted.
You also can manipulate the switch-configuration files from privileged EXEC (enable) mode. Remember that two configuration files exist at all times—running-config and startup-config. Any configuration changes that you make to a switch are applied immediately to the running-config file. The only way to update the startup-config is by manually copying another file to it. Cisco IOS Software allows the following commands to manipulate the configuration files:
- copy running-config startup-config—The contents of the running-config are copied into the startup-config, replacing any similar commands there. After this is done, any dynamic configuration changes are saved and are preserved across power failures or switch reloads. (This command should be used regularly to save any new configuration changes. Use it prudently if you need to back out a large number of changes.)
- copy startup-config running-config—The permanent contents of the startup-config file are copied into the running-config, replacing any similar commands there. The entire runningconfig is not simply overwritten; the startup-config commands are copied over while any other existing running-config commands are kept active. This operation is performed as a switch boots up. (This command quickly can restore a misconfigured switch to a known state.)
- copy running-config tftp:—A switch’s current running configuration is copied to a TFTP server. The server address and destination filename are prompted. Use this command to store a backup snapshot copy of the switch configuration.
- copy tftp: startup-config—When a switch configuration is lost or needs to be restored to a known state, a backup copy of the configuration is copied from a TFTP server to the startupconfig file. The new changes do not take effect until the switch is reloaded or until the startupconfig is copied to the running-config. (You also could use copy tftp: running-config, but this would make immediate configuration changes as commands from the TFTP file are copied over. Use caution so that your configuration changes occur under controlled circumstances.)
- erase startup-config—The entire contents of the startup-config file are erased. Use this command when a switch has been retired from one function and needs to be relocated or completely reconfigured.
Troubleshooting from the Operating System
The Cisco Catalyst IOS Software provides many commands that can verify or troubleshoot a switch in its current environment. Sometimes you might wonder what software image or configuration commands are being used by a switch. A switch also can produce real-time debugging information about a feature or condition to aid in troubleshooting. Information is also available to help identify other neighboring Cisco devices in a network. This section explains each of these tasks and how to accomplish them using the relevant commands.
Displaying Configuration and File Contents
Cisco IOS Software offers many commands that you can use from the EXEC mode command line to display the contents of files, current configuration states, and values for troubleshooting. You can use the following commands to view and troubleshoot switch files and file systems:
- show version—Displays the current version of Cisco IOS Software running in a switch, along with many details about available hardware, RAM and Flash memory, switch uptime, the current running IOS image file, the reason for the last reload, and the configuration register’s contents.
- show running-config [interface type mod/num | vlan vlan-id | module mod]—Displays the contents of the running-config configuration file. You can jump to the relevant configuration of a specific interface, VLAN, or switch module, if desired.
- show startup-config—Displays the startup-config configuration file contents.
- show tech-support—Provides information to Cisco TAC support personnel; almost every known bit of information about the switch is displayed. Be sure to configure your terminal emulator to capture text to a file before issuing this command.
- verify flash:filename—Verifies the checksum of the Flash file filename. This can ensure that an IOS image is not corrupted after it has been copied into Flash memory. (During the actual copy process, the checksum automatically is verified. You can use the verify command to make sure that the file has not become corrupted since it was copied originally.)
- more filesystem:filename—Displays the contents of a plain-text file from the command line. This can be useful when you need to read configuration files that have been stored in a Flash file system. You also can view text files that are stored on a remote TFTP server—from the IOS command line.
When a large amount of output is displayed, the switch usually shows a page at a time, pausing with a “-More-” prompt. You can press either the Space key to display the next page, the Return (Enter) key to display the next line, or /text to search forward and begin the page of output at the line containing text. Using the slash key allows a quick search within the context of the entire output.
Debugging Output
For more focused and real-time information about a certain switch feature, you can use the debug EXEC command. Debug output is not used normally, unless you suspect a problem with a feature or an interaction with other switches in the network.
You can use many options with the debug command, each pertaining to a switch feature or a specific activity. Type the debug command followed by ? to get context-based help on all the supported debugging commands and keywords. After you enable a debug command, you can see the debug output listed as events occur on the switch.
CAUTION Use the debug commands cautiously because they can generate a tremendous amount of output. Not only can this display slowly on a serial console connection, but the debug process itself also can bog down the switch CPU to the point that it severely impacts traffic forwarding.
Always be sure to turn off any debugging commands when you finish with them by using the no debug options command, where the options keywords match the ones you used to enable debugging. To quickly disable all active debugging commands, use the no debug all or undebug all commands.
Viewing CDP Information
To view information learned from CDP advertisements of neighboring Cisco devices, use one of the following commands:
Switch# show cdp interface [ type mod/num] Switch# show cdp neighbors [ type mod/num | vlan vlan-id] [ detail]
The first command displays CDP information pertaining to a specific interface. If the type, module, and port information is omitted, CDP information from all interfaces is listed. The second command displays CDP information about neighboring Cisco devices. A specific interface or VLAN can be given to display only neighbors connected to it. Using the detail keyword results in
the display of all possible CDP information about each neighbor.
Recall that CDP messages are sent out every 60 seconds, and all entries received are placed in a cache. The cache is updated with new entries, and stale entries are aged out after a hold time of 180 seconds. If you suspect a problem with a neighboring switch, you might want to clear the CDP cache of all potentially stale information to see what new information is being received from neighbors. Do this with the clear cdp table command.
As demonstrated in Example 4-1, the show cdp neighbors and the show cdp neighbors detail commands can be useful when you are connected to a switch and need to know more about what other switches are nearby in a network. Particularly useful are the IP address entries, allowing Telnet access to previously unknown switches. To see a brief listing of only the neighbor switch names and their management IP addresses, use the show cdp entry * protocol command.
Example 4-1 Displaying CDP Information for Neighboring Devices
Switch# show cdp neighbors Capability Codes: R - Router, T - Trans Bridge, B - Source Route Bridge S - Switch, H - Host, I - IGMP, r - Repeater Device ID Local Intrfce Holdtme Capability Platform Port ID BuildingA-1 Gig 2/1 158 S I WS-C3550-4Gig 0/1 CoreSwitch-1 Gig 1/1 158 T S Cat 6000 Gig 3/1 Switch# show cdp neighbors gig 1 /1 detail ------------------------- Device ID: CoreSwitch-1 Entry address(es): IP address: 192.168.199.9 Platform: cisco Catalyst 6000, Capabilities: Router Switch IGMP Interface: GigabitEthernet1/1, Port ID (outgoing port): GigabitEthernet3/1 Holdtime : 136 sec Version : Cisco Internetwork Operating System Software IOS (tm) c6sup2_rp Software (c6sup2_rp-JK9SV-M), Version 12.2(14)SY4, EARLY DEPLOYMENT RELEASE SOFTWARE (fc1) Technical Support: http://www.cisco.com/techsupport Copyright 1986-2004 by cisco Systems, Inc. Compiled Wed 31-Mar-04 10:50 by kellmill Switch# show cdp entry * protocol Protocol information for BuildingA-1 : IP address: 192.168.199.107 Protocol information for CoreSwitch-1 : IP address: 192.168.199.9 Switch#