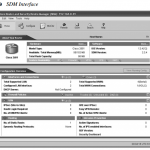
Securing the Router Locking Down the Router This section begins by identifying router services that are susceptible to attack and by explaining how security can be compromised by various router management services. You will learn two approaches for hardening a Cisco IOS router against attacks: Using Cisco SDM’s One-Step Lockdown feature Using the auto secure CLI … [Read more...]
Configuring AAA
Configuring AAA Configuring AAA Using the Local User Database Unauthorized access to a network creates the potential for network intruders to gain access to sensitive network equipment and services. The Cisco AAA architecture provides a means to address this threat through systematic, scalable access security. Of course, network users and would-be intruders are not the only … [Read more...]
CCNA Collaboration 210-060 CICD and 210-065 CIVND Complete Video Course
CCNA Collaboration 210-060 CICD and 210-065 CIVND Complete Video Course https://www.youtube.com/watch?v=hRnUmPOs724&list=PL9UP_4zHScPymlvLs2AW20Zs5VfCMEu0x https://goo.gl/DnUA9r For More CCNA study Material, Please click here … [Read more...]
Defending the Perimeter
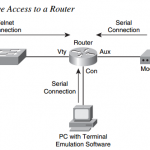
Defending the Perimeter ISR Overview and Providing Secure Administrative Access This section begins by introducing the security features offered in the Cisco line of ISR routers. Additional hardware options for these routers are also discussed. Then, with a foundational understanding of the underlying hardware, you will learn a series of best practices for security … [Read more...]
Developing a Secure Network
Developing a Secure Network Increasing Operations Security After a network is installed, network operations personnel monitor and maintain it. From a security perspective, operations security attempts to secure hardware, software, and various media while investigating anomalous network behavior. System Development Life Cycle A computer network is a dynamic entity, … [Read more...]
Network Security Principles
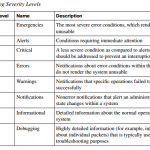
Network Security Principles Exploring Security Fundamentals A “secure network” is a moving target. As new vulnerabilities and new methods of attack are discovered, a relatively unsophisticated user can potentially launch a devastating attack against an unprotected network. This section begins by describing the challenges posed by the current security landscape. You will learn … [Read more...]
STP Manipulation Attack Mitigation Steps
STP Manipulation Attack Mitigation Steps EXAM ALERT Stop! If you are unfamiliar with spanning tree protocol (STP) operation, now is the time for you to review the subject from the CCNA prerequisite material. Pay particular attention to the role of the root bridge in the spanning tree, as well as the role that Bridge Protocol Data Units (BPDUs) play in electing the root … [Read more...]
CCNA Data Center DCICT 200-155 Complete Video Course
CCNA Data Center DCICT 200-155 Complete Video Course https://www.youtube.com/watch?v=QMe8ZgviyZ4&list=PL9UP_4zHScPwrrIVgNHW8c2weI-pIgFDL https://goo.gl/jEJ3xj For More CCNA study Material, Please click here … [Read more...]
CCNA 200-125 Exam: Basic Questions With Answers
CCNA 200-125 Exam Questions and Answers CCNA Practice Test 200-125 Dumps Exam Questions and Answers 2019-2020 Pdf Free Online download Question 1. Which network topology allows all traffic to flow through a central hub? A. bus B. star C. mesh D. ring Answer: B Question 2. What is true about Ethernet? (Choose two) A. 802.2 Protocol B. 802.3 Protocol C. 10BaseT … [Read more...]
Miscellaneous Switch Security Features
Miscellaneous Switch Security Features Following is a high-level discussion of some additional switch security features that can be used by themselves or in conjunction with the mitigation techniques previously examined Intrusion Notification In some situations, you might want to configure the switch to send a notification to an SNMP NMS when MAC addresses are learned by … [Read more...]