Designing a Cryptographic Solution Introducing Cryptographic Services To understand cryptographic services, first you must understand the science of cryptology, which in essence is the making and breaking of secret codes. Cryptology can be broken into two distinct areas: cryptography and cryptanalysis. Cryptography is the development and use of codes. Cryptanalysis is all … [Read more...]
CCNP Security FAQ: Identity Management
CCNP Security FAQ: Identity Management Figure ISE identity source sequence configuration Q1. What are two types of identities used in Cisco Identity Service Engine? a. SSID b. MAC address c. Username d. IP address Answer: B, C. An identity is a representation of who a user or device is. Cisco ISE uses an endpoint’s MAC address to uniquely identify that endpoint. A … [Read more...]
Using Cisco IOS IPS to Secure the Network
Using Cisco IOS IPS to Secure the Network Examining IPS Technologies Although IDS and IPS perform similar functions, this section explores how these network security solutions differ. Various approaches to detecting and preventing an intrusion are discussed. This section also explores signatures and how they can trigger an alarm. This section concludes by discussing best … [Read more...]
Using Cisco IOS Firewalls to Defend the Network
Using Cisco IOS Firewalls to Defend the Network Exploring Firewall Technology Securing all aspects of your network can be a daunting task. For an organization with ecommerce, intranet, and extranet sites, as well as e-mail, this only adds to the complexity of the task. Of course, there are costs to providing a high level of security, in terms of both staff and equipment … [Read more...]
Exploring Secure Voice Solutions
Exploring Secure Voice Solutions Defining Voice Fundamentals This section begins by defining voice over IP and considering why it is needed in today’s corporate environment. Because voice packets are flowing across a data infrastructure, various protocols are required to set up, maintain, and tear down a call. This section defines several popular voice protocols, in addition … [Read more...]
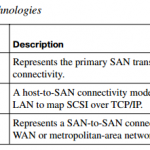
Providing SAN Security
Providing SAN Security Overview of SAN Operations Organizations are producing ever-increasing amounts of data. A storage-area network (SAN) is an effective means to allow them to store and access this data in a secure fashion. This section examines the fundamentals of SAN operation and describes the technology behind these focused networks. It also examines attacks focused on … [Read more...]
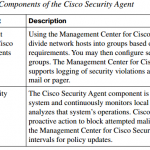
Implementing Endpoint Security
Implementing Endpoint Security Examining Endpoint Security To devise a successful strategy to defend your endpoints, you must begin with knowledge of the defenses that are available. This section describes the current endpoint protection methods, such as Host-based Intrusion Prevention System (HIPS), integrity checkers, operating system protection, and the Cisco NAC … [Read more...]
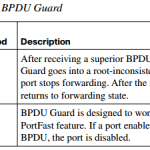
Securing Layer 2 Devices
Securing Layer 2 Devices Defending Against Layer 2 Attacks This section begins by exploring the nature of Layer 2 switch operation and why it is such an attractive target for attackers. Then, approaches for mitigating a variety of Layer 2 attacks are addressed. These strategies include best practices for securing a Layer 2 network, protecting against VLAN hopping attacks, … [Read more...]
CCNA Cloud CLDADM 210-455 Complete Video Course
CCNA Cloud CLDADM 210-455 Complete Video Course https://www.youtube.com/watch?v=GjD27VyOYEQ&list=PL9UP_4zHScPz35gaincmzptwnH1cBM8Oj https://goo.gl/7tMtNs For More CCNA study Material, Please click here … [Read more...]
CCNA Cloud CLDFND 200-451 Complete Video Course
CCNA Cloud CLDFND 200-451 Complete Video Course https://www.youtube.com/watch?v=C3SdnXLAA7M&list=PL9UP_4zHScPy8PX3z55iFF0rW66n-1PDf https://goo.gl/shSqW3 For More CCNA study Material, Please click here … [Read more...]