CCNP Voice FAQ: WLAN Management Q1. The Cisco Unified Wireless Network unique approach addresses all layers of the WLAN network through what five interconnected elements? A. Access points, mobility platform, network unification, world-class network management, and unified advanced services B. Client devices, access points, mobility platform, network unification, and … [Read more...]
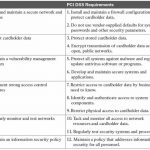
CCNA Cyber Ops FAQ: Compliance Frameworks
CCNA Cyber Ops FAQ: Compliance Frameworks Q1. PCI DSS is designed to ensure which of the following? A. Protect electronic health care information B. Protect financial data such as the PAN, account data on a magnetic strip, and data on embedded chips C. Prevent data loss D. Prevent corporate fraud Answer: B. PCI DSS is designed to protect financial transactions, meaning … [Read more...]
CCNP Secure IPS FAQ: Cisco IDS Network Module for Access Routers
CCNP Secure IPS FAQ: Cisco IDS Network Module for Access Routers Q1. What is the maximum amount of traffic that the network module can examine? A. 85 Mbps B. 45 Mbps C. 60 Mbps D. 100 Mbps E. 150 Mbps Answer: B Q2. How many external interfaces are on the network module? A. No external ports B. 1 Ethernet port C. 1 Ethernet port and 1 console port D. 1 console … [Read more...]
CCNP Voice FAQ: Classification, Marking, and NBAR
CCNP Voice FAQ: Classification, Marking, and NBAR Q1. Which of the following is not a valid classification traffic descriptor? A. Incoming interface B. Traffic path C. IP precedence or DSCP value D. Source or destination address Answer: B Q2. Which of the following is not considered a data link layer QoS marking field? A. CoS B. Frame Relay DE C. DSCP D. ATM … [Read more...]
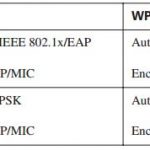
CCNP Voice FAQ: Introducing 802.1x and Configuring Encryption and Authentication on Lightweight Access Points
CCNP Voice FAQ: Introducing 802.1x and Configuring Encryption and Authentication on Lightweight Access Points Q1. Which of the following is not an issue or a weakness of initial WLAN security approaches? A. Relying on SSID as a security measure B. Relying on MAC filters C. Overhead of mutual authentication between wireless clients and access control/authentication … [Read more...]
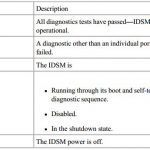
CCNP Secure IPS FAQ: Cisco IDS Module (IDSM)
CCNP Secure IPS FAQ: Cisco IDS Module (IDSM) Q1. What is the maximum amount of traffic that the IDSM-2 can monitor? A. 500 Mbps B. 450 Mbps C. 600 Mbps D. 250 Mbps E. 1000 Mbps Answer: C Q2. Which of the following is false about the IDSM-2? A. It has the ability to monitor multiple VLANs. B. It impacts the switch performance. C. It runs the same code base as the … [Read more...]
CCNA Cyber Ops FAQ: Incident Response Teams
CCNA Cyber Ops FAQ: Incident Response Teams Q1. Which of the following are examples of some of the responsibilities of a corporate CSIRT and the policies it helps create? (Select all that apply.) A. Scanning vendor customer networks B. Incident classification and handling C. Information classification and protection D. Information dissemination E. Record retentions and … [Read more...]
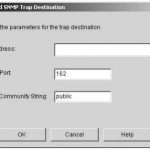
CCNP Secure IPS FAQ: Verifying System Configuration
CCNP Secure IPS FAQ: Verifying System Configuration Q1. Which of the following is not provided in the output of the show version sensor CLI command? A. Sensor uptime B. Recovery partition software version C. Sensor host name D. Current sensor software version E. Previous sensor software version Answer: C Q2. Which of the following is not one of the sections of the … [Read more...]
CCNP Voice FAQ: Wireless LAN QoS Implementation
CCNP Voice FAQ: Wireless LAN QoS Implementation Q1. Select the correct statement about wireless LANs. A. WLANs are mostly implemented as extensions to wired LANS. B. WLANs are occasionally implemented as overlays to wired LANs. C. WLANs are sometimes implemented as substitutes for wired LANs. D. All of the above. Answer: D Q2. Which statement is true about 802.11 … [Read more...]
CCNA Cyber Ops FAQ: Introduction to Incident Response and the Incident Handling Process
CCNA Cyber Ops FAQ: Introduction to Incident Response and the Incident Handling Process Q1. What NIST special publication covers the incident response process? A. Special Publication 800-61 B. Judiciary, private, and individual investigations C. Public, private, and corporate investigations D. Government, corporate, and private investigations Answer: A. NIST’s Special … [Read more...]