CCNP Secure IPS FAQ: Cisco Intrusion Prevention System (IPS) Overview Q1. What do you call a signature that does not fire after observing normal user traffic? A. False positive B. True negative C. False negative D. True positive Answer: B Q2. Which of the following is a valid risk rating? A. High B. Severe C. 80 D. Critical E. Catastrophic Answer: C Q3. Which … [Read more...]
CCNP Secure IPS FAQ: Alarm Monitoring and Management
CCNP Secure IPS FAQ: Alarm Monitoring and Management Q1. What is the minimum recommended amount of RAM for the Security Monitor server? A. 2 GB B. 1 GB C. 512 MB D. 256 MB E. 1.5 GB Answer: B Q2. What is the minimum recommended amount of RAM for the client systems that access Security Monitor? A. 2 GB B. 1 GB C. 512 MB D. 256 MB E. 1.5 GB Answer: D Q3. What … [Read more...]
CCNP Security VPN FAQ: Configuring Cisco VPN 3000 for Remote Access Using Digital Certificates
CCNP Security VPN FAQ: Configuring Cisco VPN 3000 for Remote Access Using Digital Certificates Q1. What Public Key Cryptography Standard (PKCS) is used to enroll with a CA? Answer: PKCS #10 is the standard form generally used to request certificate enrollment with a CA. Q2. What field in the certificate request should match the IPSec group name on the VPN … [Read more...]
CCNP Secure IPS FAQ: Cisco IPS Response Configuration
CCNP Secure IPS FAQ: Cisco IPS Response Configuration Q1. The Deny Connection Inline action stops traffic that matches which of the following descriptions (where "source" and "destination" refer to the traffic that caused the signature to trigger)? A. Source IP address and destination port B. Source IP address and destination IP address C. Source IP address, destination IP … [Read more...]
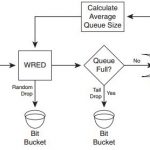
CCNP Voice FAQ: Congestion Avoidance, Policing, Shaping, and Link Efficiency Mechanisms
CCNP Voice FAQ: Congestion Avoidance, Policing, Shaping, and Link Efficiency Mechanisms Q1. Which of the following is not a tail drop flaw? A. TCP synchronization B. TCP starvation C. TCP slow start D. No differentiated drop Answer: C Q2. Which of the following statements is not true about RED? A. RED randomly drops packets before the queue becomes full. B. RED … [Read more...]
CCNA Cyber Ops FAQ: Forensics
CCNA Cyber Ops FAQ: Forensics Q1. Which of the following are the three broad categories of cybersecurity investigations? A. Public, private, and individual investigations B. Judiciary, private, and individual investigations C. Public, private, and corporate investigations D. Government, corporate, and private investigations Answer: A. The three broad categories of … [Read more...]
CCNP Voice FAQ: Cisco VoIP Implementations
CCNP Voice FAQ: Cisco VoIP Implementations Q1. Which one of the following is not a benefit of VoIP compared to traditional circuit-switched telephony? A. Consolidated network expenses B. Improved employee productivity C. Access to new communication devices D. Higher voice quality Answer: D Q2. Which one of the following is not considered a packet telephony device? A. … [Read more...]
CCNP Voice FAQ: Congestion Management and Queuing
CCNP Voice FAQ: Congestion Management and Queuing Q1. Which of the following is not a common reason for congestion? A. Speed mismatch B. Aggregation C. Confluence D. Queuing Answer: D Q2. Which of the following is a congestion management tool? A. Aggregation B. Confluence C. Queuing D. Fast Reroute Answer: C Q3. Which of the following is not a function within a … [Read more...]
CCNA Cyber Ops FAQ: Threat Analysis
CCNA Cyber Ops FAQ: Threat Analysis Q1. You must have adequate control mechanisms in order to enforce and ensure that data is only accessed by the individuals who should be allowed to access it and nobody else. Which of the following techniques can be used to prevent any attacks that could impact confidentiality? A. Secure routing protocols B. Network scanners C. … [Read more...]
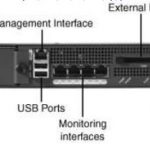
CCNP Secure IPS FAQ: Capturing Network Traffic
CCNP Secure IPS FAQ: Capturing Network Traffic Q1. Operating in inline mode requires how many sensor interfaces? A. Two B. One C. Three D. One or two E. None of the above Answer: A Q2. Which infrastructure device(s) enables your sensor to capture traffic by default? A. Switch B. Router C. Hub D. Firewall E. Switch and hub Answer: C Q3. Which switch capture … [Read more...]