Overview of VPN Technology
Virtual Private Networks (VPNs) are “virtual” in that they can either replace or, at least, complement existing network circuits, whether dial-in or between sites. VPNs are virtual in that sense, but hopefully there is nothing virtual about their privacy! According to Cisco, a good working definition of a VPN is as follows: “A VPN [is] an encrypted connection between private networks over a public network, usually the Internet.”
This is the definition that we use in this Exam Cram; although there are a number of other technologies that are called VPNs, they don’t provide for encryption and are thus hardl private. Historically, anything that created an IP tunnel was called a VPN. With such a loose definition, technologies that don’t provide encryption, such as Generic Routing Encapsulation (GRE) and IPsec tunnels using Authentication Header (AH), are still considered VPNs.
Any kind of network connection over a hostile network could benefit from implementing a VPN. Even on the inside of an organization’s perimeter, there
are often places where a VPN is required to create a secure channel between network devices, as well as between people and network devices.
Cisco VPN Products
Table 7.1 lists the primary products in the Cisco product portfolio that can be used to deploy VPNs.

VPN Benefits
VPNs have many benefits, including the following:
- Cost Savings. The use of cost-effective, high-speed Internet technologies versus dedicated WAN links makes VPNs attractive.
- Security. Advanced encryption, integrity, and authentication protocols provide for the highest protection against unauthorized access and data loss.
- Scalability. VPNs can grow seamlessly without the need to add extra infrastructure, particularly when using the Internet.
- Compatibility with Broadband Technology. VPN technology is largely independent of the underlying infrastructure, meaning that organizations can leverage on the most convenient broadband technology for the greatest flexibility.
There are two main types of VPNs:
- Site-to-site
- Remote-access
Site-to-Site VPNs
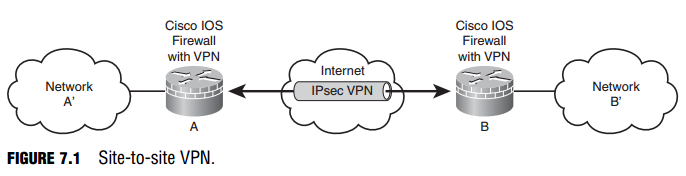
With a site-to-site VPN, host devices operate behind network devices, such as IOS routers, which act as VPN gateways. This is an evolution of WAN technology. The host devices do not need any special software because the fact that there is a VPN between sites is immaterial to them, as the VPN is established between other devices, possibly their own default gateway in the simplest case.
For example, if we configure IOS routers to be VPN gateways, the IP hosts in the production network behind the router would only have to attempt to establish a connection with a device on the inside of a peer network’s router. The host’s own VPN router would recognize that this site-to-site traffic from the local site to the remote site needs to be protected by the VPN and it would launch a tunnel (that is, the VPN) to its peer if one doesn’t already exist. This is illustrated with a small modification to the reference network layout that was first introduced in Figure 5.1 of Chapter 5, “Using Cisco IOS Firewalls to Implement a Network Security Policy.” In Figure 7.1, all traffic between the A and B networks is protected inside a siteto-site VPN between router A and router B.
A device inside network A’—the system administrator PC, for example—would already have router A as its default gateway. Something magic happens from that PC’s perspective because when it tries to communicate with the private (RFC 1918) addresses in network B’, it gets a response. Breaking it down just a little bit, this is what happens:
- Confidentiality. The IP packet from the system administrator’s PC, from network A’ to network B’, is encrypted before it is encapsulated in another IP packet to router B. Similarly, upon receipt, router B decrypts the A’ to B’ packet before delivering it to the destination host on the B network.
- Integrity. As we see in the section, “Conceptualizing a Site-to-Site IPsec VPN,” it’s possible that when the encrypted packet is sent to router B
from router A, there is some integrity information added to the packet to add some assurance that the packet has not been tampered with in transit. - Authentication. Additionally, some authentication information might have been added to the encrypted IP packet to add assurance that it actually came from router A. Remember the C-I-A triad from Chapter 1, “Network Insecurity”? The “A” in the VPN C-I-A triad stands for authentication.
The optional integrity and authentication information will add some extra overhead per unit of data transmitted. It is up to the guidelines contained in the organization’s comprehensive security policy as to whether an acceptable tradeoff has been achieved between security and performance. Many VPN implementations implement confidentiality only, relying on other layers of the OSI model to provide for integrity and authentication outside the context of the VPN.
Router B (or router A, for that matter) in Figure 7.1 could be any appropriate Cisco VPN product from Table 7.1.
Remote-Access VPNs
In the same way that site-to-site VPNs evolved from traditional WANs, remoteaccess VPNs are an evolution of dial-up networking technology. Certainly the same principles of C-I-A apply here. The two most evident differences between remote-access and site-to-site VPNs are the following:
- Remote-access VPN clients initiate the VPN on demand.
- The remote-access client (whether a PC or a Cisco hardware device) requires Cisco VPN client software to connect.
When implemented as a software solution on a remote user’s PC, this can be a very flexible solution. The teleworker can benefit from the same confidentiality, integrity, and authentication services of a site-to-site VPN, while using whatever Internet technologies are at their immediate disposal.
Referring to Figure 7.2, a corporate knowledge worker could be sipping designer coffee at their local coffee shop’s wireless hotspot while protecting corporate secrets on network A’ from hackers and the merely curious.

Cisco IOS SSL VPN
Cisco specifies another type of VPN that uses a web browser’s built-in Secure Sockets Layer (SSL) encryption to encrypt at the transport layer of the OSI model. One advantage of this solution is that in its simplest form, it doesn’t require the installation of additional software on a client PC. SSL VPN offers two modes of operation:
- Clientless. Uses a web portal to access hosts behind the gateway. Access to file and print shares, email servers, web servers, and other services is provided by the web portal’s interface.
- Client. Uses a thin client that provides an IP address and thus the ability to access applications with their native interface.
The SSL VPN solution is an emerging technology that complements Cisco’s IPsec VPN offerings. Some disadvantages of the SSL VPN solution are as follows:
- Software-Only. One disadvantage is that it is a software-only solution in IOS routers; thus, it doesn’t take advantage of the hardware-accelerated onboard encryption in many router models. The router (and the client) CPU processes all the encryption.
- Cryptographic Security. Does not currently support the same level of encryption security as IPsec.
SSL VPNs have compatibility advantages. SSL VPNs can be configured and operate alongside other features on Cisco network devices. SSL VPNs are compatible with the following:
- Dynamic Multipoint VPNs (DMVPNs)
- Cisco IOS Firewalls
- IPsec
- Intrusion Protection Systems (IPSs)
- Cisco Easy VPN (Cisco’s remote-access IPsec VPN solution)
- Network Address Translation (NAT)
Cisco VPN Product Positioning
Cisco has a number of devices in its product portfolio that provide VPN services. Some of these devices are end-of-sale (EOS) and are marked as such in Table 7.2. EOS does not mean end-of-life! For example, there are literally hundreds of thousands of PIX firewalls in the field, and Cisco continues to support these devices with new OS updates and technical support.
You should memorize Table 7.2, as Cisco just loves asking questions that refer to information found in tables.

The VPN 3000 Series Concentrator was end-of-sale (EOS) in February 2007. The PIX 500 Series Security Appliances were recently announced EOS, with the last order date being July 28, 2008. They are not end-of-life (EOL) until July 27, 2013. Our focus will be on VPN-enabled IOS routers and the ASA 5500 Security Appliances. It’s also worth noting that Cisco recently announced (Q1 2008) two new ASA 5500 Series models: the ASA 5580-20 and 5580-40. These devices are positioned at the service provider level and have option cards that augment the ASA’s built-in hardware encryption by providing VPN hardware acceleration of 10,000 IPsec and 10,000 SSL connections simultaneously. Here is a link to a product matrix for the complete ASA 5500 Series portfolio: http://www.cisco. com/en/US/products/ps6120/prod_models_comparison.html.
Here is a link to Cisco’s Q&A about the EOS PIX firewalls: http://www.cisco.com/en/US/prod/collateral/vpndevc/ps5708/ps5709/ps2030/qa_eos_for_ sale_for_cisco_pix_products_customer.html.
VPN-Enabled IOS Router Features
Here are some of the VPN features of the Cisco VPN-enabled IOS routers:
- Voice and Video Enabled VPN (V3PN). Integration of QoS, IPsec, and VoIP (IP telephony).
- IPsec Stateful Failover. Provides for network resiliency in site-to-site
VPN configurations, in both stateless and stateful failover solutions. Options include the following: - Dead Peer Detection (DPD)
- Hot Standby Router Protocol (HSRP)
- Reverse Route Injection (RRI)
- Stateful Switchover (SSO)
- DMVPN. Enables automatic provisioning of site-to-site IPsec VPNs,
putting together three Cisco IOS features: - Next Hop Resolution Protocol (NHRP)
- Multipoint GRE
- IPsec VPN
- Cisco Easy VPN. Cisco’s common framework for remote-access IPsec VPNs.
ASA 5500 Series Adaptive Security Appliance
As you can infer from Table 7.2, the primary purpose of the ASA 5500 Series security appliances is as a perimeter security device that implements the organization’s comprehensive security policy. Because the IT security staff own the policy, they also own the security appliance and any policies, including the VPN, which are configured on it. In the context of VPN technology, the ASA 5500 Series of security appliances is Cisco’s direct replacement for the 3000 Series VPN concentrators, of which many tens of thousands still exist in the field. Here are some of the features of the ASA 5500 Series of security appliances:
- Flexible Platform. IPsec and SSL VPN solutions on one platform that also supports application inspection firewall and IPS.
- Resilient Clustering. VPN load balancing and backup server in a mixed environment of ASAs and VPN concentrators.
- Cisco Easy VPN. Cisco’s common framework for remote-access IPsec VPNs. Also supports automatic Cisco VPN Client updates.
- Cisco IOS SSL VPN. Both clientless and client-based solutions.
- Web-Based Management. The Cisco Adaptive Security Device Manager (ASDM) configures and manages all the security and VPN features of the appliance.
VPN Clients
Let’s eliminate confusion here before it even begins! Cisco’s product planners have been hard at work coming up with worthy names for their VPN remoteaccess solutions, both IPsec and SSL:
- Easy VPN. If it’s a remote-access IPsec VPN solution, regardless of whether the client uses Cisco software on a PC or the client is a device such as a router, it is called Easy VPN. Of course, it would be too easy if the client was called a client! The client is called an Easy VPN Remote. The VPN server is called an Easy VPN Server. See how easy that is?
- WebVPN. If it’s a remote-access SSL VPN solution, it is called WebVPN, regardless of whether the client is a web browser accessing servers behind the server’s web portal, or a thin client such as the SSL VPN Client (SVC) or the newer standalone AnyConnect VPN Client (currently only supported on the ASA 5500 Series Adaptive Security Appliance).
Here are some Cisco VPN clients. See if you can determine which broad category, Easy VPN or Web VPN, they fall into (the answers are after the list):
- Certicom Client. IPsec VPN client software that runs on wireless PDAs with either the Palm OS or Windows Mobile operating systems.
- Cisco VPN 3002 Hardware Client. (EOS February 2007) Dedicated remote-access VPN client appliance. Connects SOHO LANs to the VPN.
- Cisco VPN Software Client. Software loaded on an individual’s PC or laptop that initiates an IPsec VPN to a central site VPN server. Comes in versions for Linux, Mac, and Windows OSs.
- Cisco AnyConnect VPN Client. SSL VPN client software loaded on an individual’s PC or laptop that initiates an SSL VPN to a central site VPN server. Currently supports Windows Vista, XP, and 2000 OSs, as well as MAC OS X (version 10.4 or later) and Red Hat Linux (version 9 or later).
Answers: Certicom Client = Easy VPN; Cisco VPN 3002 Hardware Client = Easy VPN; Cisco VPN Software Client = Easy VPN; Cisco AnyConnect VPN Client = WebVPN.
Hardware-Accelerated Encryption
Cisco offers hardware modules for modular routers, security appliances, and concentrators that will offload encryption processing from the device’s CPU and thus increase encrypted throughput:
- AIM-VPN (Advanced Integration Module). Certain modular IOS router models.
- Cisco IPsec VPN SPA (Shared Port Adapter). Catalyst 6500 Series switches and 7600 Series routers.
- SEP-E (Scalable Encryption Processor–Enhanced). VPN 3000 Series concentrators.
- VAC+ (VPN Accelerator Card +). Modular PIX Firewalls.
All ASA security appliances have onboard hardware encryption for both IPsec and SSL VPNs.
IPsec Compared to SSL
Cisco’s VPN product portfolio consists of both IPsec and SSL VPN solutions in order to give the most choices to their customers. Whether you choose IPsec or SSL for your VPN solution, there are some tradeoffs between usability and security. The AnyConnect SSL VPN solution, for example, is simple to use and tolerates very well NAT devices on the path between the client and the server. In IPsec VPN’s favor is the strong authentication that can be used to secure the communication path.
Table 7.3 is a summary that compares the two VPN technologies (SSL and IPsec) in the areas of: applications, encryption, authentication, ease of use, and overall. Memorize this table. It is sure to be on the exam. If you are reading this chapter before Chapter 6, “Introducing Cryptographic Services,” you may want to review the definitions for encryption algorithms, key length, and authentication.

There is an inconsistency in the Applications comparison in Table 7.3. As we have seen, one of Cisco’s SSL VPN solutions is the AnyConnect client. When using the AnyConnect SSL VPN client, you can have your cake and eat it too! The AnyConnect client obtains an IP address from the VPN gateway (an IOS router, for example), and you can then access applications on the VPN gateway’s network using their native interfaces. It also supports the use of digital certificates for authentication, and data can be protected up to a 256-bit AES cipher. Cisco is probably trying to incorporate the clientless Web VPN portal in their comparison because that technology has integral support for web servers, file sharing, and email.