CCNP Switch FAQ: Securing Switch Access
Q1. Which switch feature can grant access through a port only if the host with MAC address 0005.0004.0003 is connected?
a. SPAN
b. MAC address ACL
c. Port security
d. Port-based authentication
Q2. Port security is being used to control access to a switch port. Which one of these commands will put the port into the errdisable state if an unauthorized station connects?
a. switchport port-security violation protect
b. switchport port-security violation restrict
c. switchport port-security violation errdisable
d. switchport port-security violation shutdown
Q3. If port security is enabled and left to its default configuration, how many different MAC addresses can be learned at one time on a switch port?
a. 0
b. 1
c. 16
d. 256
Q4. The following commands are configured on a Catalyst switch port. What happens when the host with MAC address 0001.0002.0003 tries to connect?
switchport port-security
switchport port-security maximum 3
switchport port-security mac-address 0002.0002.0002
switchport port-security violation shutdown
a. The port shuts down.
b. The host is allowed to connect.
c. The host is denied a connection.
d. The host can connect only when 0002.0002.0002 is not connected.
Q5. What protocol is used for port-based authentication?
a. 802.1D
b. 802.1Q
c. 802.1X
d. 802.1w
Q6. When 802.1X802.1X is used for a switch port, where must it be configured?
a. Switch port and client PC
b. Switch port only
c. Client PC only
d. Switch port and a RADIUS server
Q7. When port-based authentication is enabled globally, what is the default behavior for all switch ports?
a. Authenticate users before enabling the port.
b. Allow all connections without authentication.
c. Do not allow any connections.
d. There is no default behavior.
Q8. When port-based authentication is enabled, what method is available for a user to authenticate?
a. Web browser
b. Telnet session
c. 802.1X client
d. DHCP
Q9. The users in a department are using a variety of host platforms, some old and some new. All of them have been approved with a user ID in a RADIUS server database. Which one of these features should be used to restrict access to the switch ports in the building?
a. AAA authentication
b. AAA authorization
c. Port security
d. Port-based authentication
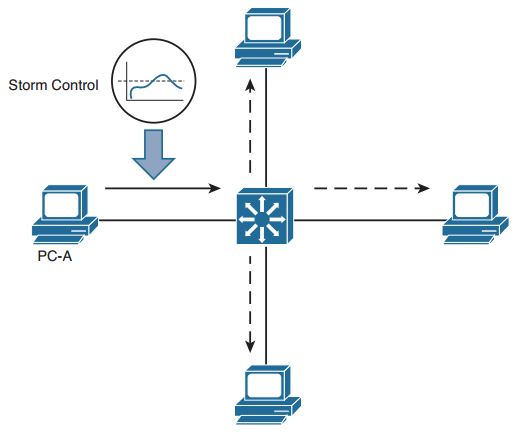
Q10. Which of the following are types of frames that Storm Control can limit before they can cause problems for hosts that are connected to a switch? (Choose all that apply.)
a. Unicast frames
b. Broadcast frames
c. Multicast frames
d. Unknown unicast frames
Q11. Suppose that an interface receives the following configuration command: storm-control broadcast level 10 Storm control will be triggered when which one of the following rising thresholds is reached?
a. At least 10 broadcast frames are received
b. At least 10 hosts are connected to a VLAN that will receive a flooded broadcast frame
c. Broadcast frames exceed 10 percent of the interface bandwidth
d. Broadcast frames exceed 10 percent of the interface MTU size
Q12. Which two of the following methods should you use to secure inbound CLI sessions to a switch?
a. Disable all inbound CLI connections.
b. Use SSH only.
c. Use Telnet only.
d. Apply an access list to the vty lines.
Q13. Suppose that you need to disable CDP and LLDP advertisements on a switch port so that untrusted devices cannot learn anything about your switch. Which one of the following answers contains the interface configuration commands that should be used?
a. cdp disable
lldp disable
b. no cdp
no lldp
c. no cdp enable
no lldp transmit
d. no cdp transmit
no lldp transmit
More Resources