CCSP SECUR FAQ : Administration of Cisco Secure Access Control Server Q1. Which of the following points do you have to consider before deploying Cisco Secure ACS? A. Dialup topology B. Number of users C. Remote access policy D. Number of Linux servers Answer: A, B, C Q2. Which of the following is the minimum CPU requirement for a Cisco Secure ACS server? A. At least a … [Read more...]
CCSP SECUR FAQ : Cisco Secure Access Control Server
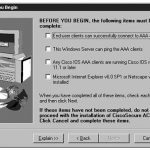
CCSP SECUR FAQ : Cisco Secure Access Control Server Q1. Which of the following devices are supported by Cisco Secure ACS? A. Cisco PIX firewall B. Cisco Network Access Servers (NAS) C. Cisco 412 D. Cisco 550 Answer: A Q2. Which of the following is true about Cisco Secure ACS? A. Centralizes access control and accounting B. Centralizes configuration management for … [Read more...]
CCSP SECUR FAQ : Configuring RADIUS and TACACS+ on Cisco IOS Software
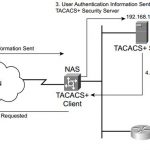
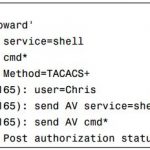
CCSP SECUR FAQ : Configuring RADIUS and TACACS+ on Cisco IOS Software Q1. Which of the following is the command to specify the TACACS+ server on the access server? A. tacacs-server host B. tacacs host C. server tacacs+ D. server host Answer: A Q2. Which is the default port that is reserved for TACACS? A. UDP 49 B. TCP 49 C. UDP 1046 D. TCP 1046 Answer: B Q3. Which … [Read more...]
CCSP SECUR FAQ : Authentication, Authorization, and Accounting
CCSP SECUR FAQ : Authentication, Authorization, and Accounting Q1. Which of the following best describes AAA authentication? A. Authentication is last defense against hackers. B. Authentication can only work with firewalls. C. Authentication is the way a user is identified prior to being allowed into the network. D. Authentication is a way to manage what a user can … [Read more...]
CCSP SECUR FAQ : Authentication
CCSP SECUR FAQ : Authentication Q1. Which of the following is true? (Choose two.) A. Authentication provides a method for verifying the identity of users. B. NAS cannot provide authentication. C. Usernames and passwords can be stored on NAS. D. Cisco does not support RADIUS. Answer: A, C Q2. Which of the following is the least secure method of authentication? (Choose … [Read more...]
CCSP SECUR FAQ : Secure Router Administration
CCSP SECUR FAQ : Secure Router Administration Q1. What are some of the steps that can be taken to secure the console interface on a router or switch device? A. Administratively shut down the console interface. B. Physically secure the device. C. Apply an access list using the access-class command. D. Configure a console password. Answer: A, C, D Q2. How many characters … [Read more...]
CCSP SECUR FAQ : Basic Router Management
CCSP SECUR FAQ : Basic Router Management Q1. What router configuration mode do you enter by default when connecting to a router? A. Console B. ROM monitor C. User EXEC D. Privileged EXEC E. None of the above Answer: C Q2. Which IOS firewall feature enables you to inspect traffic at multiple layers of the ISO model? A. Multilayer inspection B. Context-based access … [Read more...]
CCSP SECUR FAQ : Defense in Depth
CCSP SECUR FAQ : Defense in Depth Q1. What is the major concern with having a compromised host on the internal network? A. It will make the security administrator look bad. B. Data on that host can be copied. C. Data on that host can be corrupted. D. The host can be used to launch attacks against other hosts on the network. E. None of the above. Answer: D Q2. What are … [Read more...]
CCSP SECUR FAQ : Attack Threats Defined and Detailed
CCSP SECUR FAQ : Attack Threats Defined and Detailed Q1. Your boss insists that it is fine to use his wife’s name as his password, despite the fact that your security policy states that this is not a sufficient password. What weaknesses are revealed? A. This shows a lack of an effective security policy (policy weakness). B. This shows a technology weakness. C. This shows a … [Read more...]
CCSP SECUR FAQ : Network Security Essentials
CCSP SECUR FAQ : Network Security Essentials Q1. Which of the following should be included in the security policy? A. Capabilities of the firewall B. Manufacturer of the firewall C. User responsibilities D. Sanctions for violating the policy E. A network diagram F. Routing protocols used Answer: A, C, D, E Q2. Which of the following employees should have access to a … [Read more...]