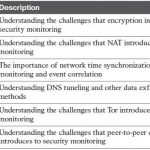
CCNA Cyber Ops FAQ: Security Monitoring Operational Challenges Q1. Which of the following are benefits of encryption? A. Malware communication B. Privacy C. Malware mitigation D. Malware identification Answer: B. Privacy is one of the main benefits of encryption. The rest of the answers are either not valid or not a benefit. Q2. Why can encryption be challenging to … [Read more...]
CCNA Cyber Ops FAQ: Network and Host Telemetry
CCNA Cyber Ops FAQ: Network and Host Telemetry Q1. Why you should enable Network Time Protocol (NTP) when you collect logs from network devices? A. To make sure that network and server logs are collected faster. B. Syslog data is useless if it shows the wrong date and time. Using NTP ensures that the correct time is set and that all devices within the network are … [Read more...]
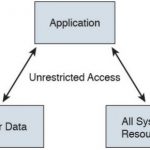
CCNA Cyber Ops FAQ: Endpoint Security Technologies
CCNA Cyber Ops FAQ: Endpoint Security Technologies Q1. What is a Trojan horse? A. A piece of malware that downloads and installs other malicious content from the Internet to perform additional exploitation on an affected system. B. A type of malware that executes instructions determined by the nature of the Trojan to delete files, steal data, and compromise the integrity … [Read more...]