Configuring PPP
Objectives:
- Configure and verify a basic WAN serial connection
- Configure and verify a PPP connection between Cisco routers
The configuration of PPP without any options does not even deserve its own section. All you need to do is access the interface you would like to enable to run PPP and type the command encapsulation ppp. After you do that on both sides of the connection, you’re finished. For example, if I wanted to configure PPP on the Serial 0 interface of a router, here is the process:
AccessServer#configure terminal Enter configuration commands, one per line. End with CNTL/Z. AccessServer(config)#interface serial 0 AccessServer(config-if)#encapsulation ppp
After you begin turning on the options, the configuration can get a little more complex. This chapter discusses turning on PPP authentication and compression technology.
Authentication
The CCNA exam focuses on configuring PPP authentication between two Cisco routers rather than using authentication for dial-up users (this is covered in the Building Cisco Remote Access Networks CCNP course). Typically, when Cisco routers are performing authentication on a WAN link, the routers will be configured as two-way authentication. Two-way authentication means that both routers authenticate each other. Typically, when a dial-up user connects to a router, one-way authentication is performed (the user must authenticate to the Cisco router, not vice-versa).
To set up CHAP PPP authentication, you must do the following:
- Turn on PPP encapsulation.
- Configure the necessary hostname for the authenticating routers.
- Create user accounts on each side of the connection.
- Turn on CHAP PPP authentication.
At first, these steps may seem somewhat cryptic, but let me walk you through a configuration example and explain how all these pieces fit together. Refer to Figure 22.3 for a visual of this example configuration.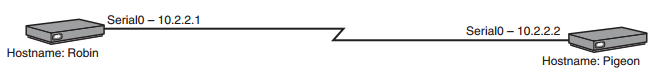
FIGURE 22.3 PPP authentication example.
This sample configuration enables two-way, CHAP PPP authentication between the Robin and Pigeon routers. For the sake of brevity, assume the router hostnames are already configured and PPP encapsulation has been enabled under the serial interfaces. Before you begin, you need to understand the significance of the router hostname. By default, when a Cisco router attempts to authenticate with another router, it uses the router hostname as its PPP username to authenticate with the other side. In this example, the router with the hostname “Robin” crosses the PPP link and attempts to authenticate with the Pigeon router, using the username “Robin.” The Pigeon router attempts to authenticate with the Robin router, using the username “Pigeon.” You therefore need to create user accounts on each router that match the usernames the routers will use when authenticating. The following syntax accomplishes this:
Pigeon#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Pigeon(config)#username Robin password cisco Robin#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Robin(config)#username Pigeon password cisco
Now, when the Robin router comes over to the Pigeon router and says “My username is Robin,” the Pigeon router has a user database that identifies that username. Likewise, the Pigeon router can now authenticate the Robin router. If you have any experience with Windows administration, this is an identical concept to creating user accounts for people to log on to their PCs.
CAUTION
The CHAP username and passwords are both case sensitive. If the hostname of your router begins with a capital letter, ensure you create the user account the same way.
When using CHAP authentication, you must use the same password for both user accounts. In this case, both the Pigeon and Robin router share the password “cisco.” It must remain the same on both sides because CHAP never actually sends the password across the wire; it sends only the MD5 hash version of it. When the receiving side gets the hash, it runs the MD5 algorithm on its own password and compares the two hashes. If they match, authentication succeeds. The following is the complete configuration of both the Pigeon and Robin routers to enable CHAP PPP authentication:
Pigeon#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Pigeon(config)#username Robin password cisco Pigeon(config)#interface serial 0 Pigeon(config-if)#encapsulation ppp Pigeon(config-if)#ppp authentication chap Robin#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Robin(config)#username Pigeon password cisco Robin(config)#interface serial 0 Robin(config-if)#encapsulation ppp Robin(config-if)#ppp authentication chap
EXAM ALERT
Be prepared to configure a PPP encapsulated, CHAP authenticated leased line connection in an exam environment. Be absolutely sure you understand that the passwords must be the same on both routers when configuring CHAP authentication.
Compression
Enabling PPP compression is a piece of cake. You just have to make sure that both sides of the connection enable it; if only one side of the connection enables it, the link fails. Using the Pigeon and Robin scenario again, the following shows the steps you can take to enable compression:
Pigeon#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Pigeon(config)#interface serial 0 Pigeon(config-if)#compress ? mppc MPPC compression type predictor predictor compression type stac stac compression algorithm <cr>
That’s it! Just use the compress command and type the mode of compression you would like to use, and let the bandwidth savings begin.