CCNP Security FAQ: Bring Your Own Device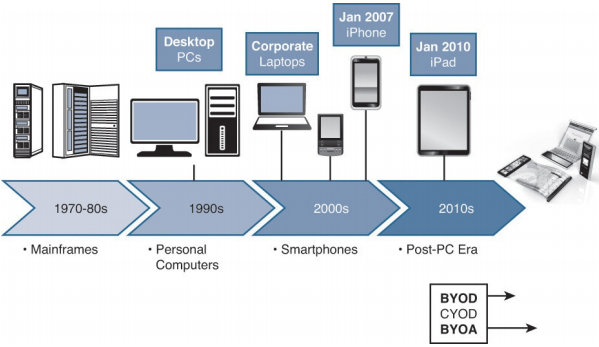
Figure: BYOD timeline.
Q1. What is the process of onboarding as it relates to BYOD?
a. It’s a form of torture used in military interrogations.
b. It prepares an endpoint for network access with supplicant configuration, and possibly even certificate provisioning.
c. It’s the process in which an IT department will prestage an endpoint for corporate use before issuing the endpoint to the end user.
d. It prepares an endpoint for network access by preconfiguring an installation package that the end user runs with administrator privilege to configure the endpoint.
Q2. With a single-SSID model for BYOD onboarding, how does the supplicant begin using its new certificate-based credentials?
a. The endpoint will continue to use the initial credentials until the next reauthentication interval.
b. ISE will send a CoA-DM, causing a new authentication.
c. ISE will send a CoA-Reauth, causing a new authentication.
d. The endpoint will continue to use the initial credentials until the endpoint is deassociated from the network and reassociates.
Q3. With dual-SSID onboarding, what stops a guest user from receiving a certificate and a supplicant profile?
a. It is hard-coded in ISE to not permit a guest user to enter the provisioning flow.
b. It’s a configurable option, so nothing prevents guests from receiving the certificate and supplicant profile.
c. It’s a configurable option based on the authorization result given to the user.
d. It’s a configurable option in the client provisioning policies to permit guests to enter the provisioning flow.
Q4. The same ACL can be used for all endpoints to be onboarded. However, the security of the ACL needs to be relaxed for Androids. What is that reason?
a. Google just feels that it is so special, so Androids require special access to keep up.
b. Androids require access to the local app store in ISE.
c. Because Android is inherently an insecure operating system, it therefore needs a less secure ACL.
d. Androids require access to their app store to download and execute Cisco’s Network Setup Assistant APP.
Q5. What are an ISE admin’s options for dealing with endpoints that are not supported by the BYOD onboarding process?
a. Cisco ISE will reject an authentication from any endpoint that cannot go through the onboarding process.
b. The admin has configurable choices to deny access to any nonconfigured endpoint that reaches the supplicant provisioning flow or to leave it in the current authorization state.
c. Cisco ISE will automatically permit access to any device that can’t be onboarded.
d. After the BYOD onboarding flow is enabled, every device must be onboarded. There are custom templates to be able to push profiles to any device that is not natively supported.
Q6. From where does an iOS-based device download the iOS Network Setup Assistant?
a. From the Apple App Store.
b. iOS uses the native OTA functionality.
c. From ISE directly.
d. From the Cisco App Store.
Q7. True or False? The ISE admin may log in to the MyDevices portal to manage all the registered devices.
a. True
b. False
Q8. Which of following lists most accurately describes the portions of BYOD onboarding that can be verified within Live Log?
a. An entry will exist for the initial authentication, CoA, and final authentication.
b. An entry will exist for the initial authentication, successful launch of the NSA app, and the final authentication.
c. An entry will exist for the initial authentication, successful endpoint registration, download of the NSA app, and the final authentication.
d. An entry will exist for the initial authentication, successful endpoint registration, CoA, and the final authentication.
Q9. As it relates to ISE 1.2, from where do Windows and Mac OSX endpoints download their Network Setup Assistant applications?
a. Windows downloads the NSA app from the Microsoft App Store. Mac OSX uses the native OTA.
b. Neither Windows nor Mac use NSA; they use native capabilities instead.
c. Windows uses native capabilities, but the Mac will use a Java applet downloaded from the CPP.
d. Windows and Mac will use a Java applet that is downloaded from the CPP hosted on ISE.
Q10. At which one of the following locations does an ISE admin determine which NSP to send to a client based on any number of attributes, including operating system?
a. Policy > Onboarding
b. Policy > Client Provisioning Policy
c. Policy > Policy Elements > Results > Client Provisioning
d. Policy > BYOD