210-451 CCNA Cloud CLDFND FAQ – Block Storage Technologies
Q1. Which of the following is a correct statement?
a. HDDs are considered primary storage.
b. DVD drives are considered secondary storage.
c. Tape libraries are considered tertiary storage.
d. RAM is not considered primary storage.
Q2. Which of the following represents data addressing in HDDs?
a. Bus/target/LUN
b. World Wide Name
c. Cylinder/head/sector
d. Domain/area/port
Q3. Which option describes an incorrect RAID level description?
a. RAID 0: Striping
b. RAID 1: Mirroring
c. RAID 6: Striping, double parity
d. RAID 10: Striping, multiple parity
Q4. Which of the following is not an array component?
a. SATA
b. Controller
c. JBOD
d. Disk enclosure
e. Access ports
Q5. Which of the following devices can potentially deploy volume thin provisioning? (Choose all that apply.)
a. JBOD
b. Storage array
c. Server
d. Dedicated appliance
e. HDD
Q6. Which of the following are block I/O access methods? (Choose all that apply.)
a. ATA
b. SCSI
c. SAN
d. NFS
e. SQL
Q7. Which of the following options is incorrect?
a. FC-0: Physical components
b. FC-1: Frame transmission and signaling
c. FC-3: Generic services
d. FC-4: ULP mapping
Q8. Which of the following is correct concerning Fibre Channel addressing?
a. WWNs are used for logical addressing.
b. FCIDs are used for physical addressing.
c. WWNs are used in Fibre Channel frames.
d. FSPF is used to exchange routes based on domain IDs.
e. FCIDs are assigned to N_Ports and F_Ports.
Q9. Which of the following is an accurate list of common SAN topologies?
a. Collapsed core, spine-leaf, core-aggregation-access
b. Collapsed core, spine-leaf, core-distribution-access
c. Collapsed core, core-edge, core-aggregation-access
d. Collapsed core, core-edge, edge-core-edge
e. Collapsed core, spine-leaf, edge-core-edge
Q10. Which of the following is not an advantage for the deployment of VSANs?
a. Interoperability
b. Multi-tenancy
c. Zoning replacement
d. Security
e. Isolation
Q11. Which of the following is incorrect about iSCSI?
a. Standardized in IETF RFC 3720.
b. Employs TCP connections to encapsulate SCSI traffic.
c. Employs TCP connections to encapsulate Fibre Channel frames.
d. Deployed by iSCSI initiators, iSCSI targets, and iSCSI gateways.
e. Initiators and targets are usually identified through IQN.
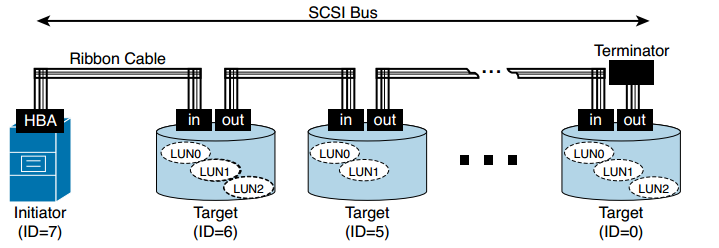
Figure: SCSI Parallel Topology
Q12. Which is the most popular block I/O access method for cloud offerings of Storage as a Service?
a. Fibre Channel
b. iSCSI
c. FCIP
d. iFCP
e. NFS
More Resources