CCNA 200-125 Exam: IP Address Questions With Answers Question 1. Which two statements about IPv4 multicast traffic are true? (Choose two) A. It burdens the source host without affecting remote hosts. B. It uses a minimum amount of network bandwidth. C. It is bandwidth-intensive. D. It simultaneously delivers multiple streams of data. E. It is the most efficient way to … [Read more...]
CCNA 200-125 Exam: CDP and LLDP Questions With Answers
CCNA 200-125 Exam: CDP and LLDP Questions With Answers Question 1. Which command would you configure globally on a Cisco router that would allow you to view directly connected Cisco devices? A. cdp run B. enable cdp C. cdp enable D. run cdp Answer: A Question 2. Which statement about LLDP is true? A. It is a Cisco proprietary protocol. B. It is configured in global … [Read more...]
CCNA 200-125 Exam: DMVPN Questions With Answers
CCNA 200-125 Exam: DMVPN Questions With Answers Question 1. Which type of topology is required by DMVPN? A. ring B. full mesh C. hub-and-spoke D. partial mesh Answer: C Question 2. Which circumstances can cause a GRE tunnel to be in an up/down state? (Choose three) A. The tunnel interface IP address is misconfigured. B. The tunnel interface is down. C. A valid route … [Read more...]
CCNA 200-125 Exam: MPLS Questions With Answers
CCNA 200-125 Exam: MPLS Questions With Answers Question 1. Which statement about MPLS is true? A. It operates in Layer 1. B. It operates between Layer 2 and Layer 3. C. It operates in Layer 3. D. It operates in Layer 2. Answer: B Question 2. What’s are true about MPLS? A. It use a label to separate traffic from several costumer B. It use IPv4 IPv6 C. other D. … [Read more...]
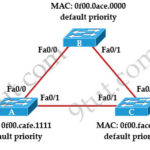
CCNA 200-125 Exam: STP Questions With Answers
CCNA 200-125 Exam: STP Questions With Answers Question 1. Refer to the topology shown in the exhibit. Which ports will be STP designated ports if all the links are operating at the same bandwidth? (Choose three) A. Switch A – Fa0/0 B. Switch A – Fa0/1 C. Switch B – Fa0/0 D. Switch B – Fa0/1 E. Switch C – Fa0/0 F. Switch C – Fa0/1 Answer: B C D Question 2. If the … [Read more...]
CCNA 200-125 Exam: WAN Questions and Answers
CCNA 200-125 Exam: WAN Questions and Answers Question 1. Which command can you enter to determine whether serial interface 0/2/0 has been configured using HDLC encapsulation? A. router#show platform B. router#show ip interface s0/2/0 C. router#show interfaces Serial 0/2/0 D. router#show ip interface brief Answer: C Question 2. Which Layer 2 protocol encapsulation type … [Read more...]
CCNA 200-125 Exam: OSI and TCP/IP Model Questions With Answers
CCNA 200-125 Exam: OSI and TCP/IP Model Questions With Answers Question 1. Which statements correctly describe steps in the OSI data encapsulation process? A. The transport layer divides a data stream into segments and may add reliability and flow control information. B. The data link layer adds physical source and destination addresses and an FCS to the segment. C. Packets … [Read more...]
CCNA Wireless 200-355 Complete Video Course
CCNA Wireless 200-355 Complete Video Course https://www.youtube.com/watch?v=yNnGavnlTZ0&list=PL9UP_4zHScPweZMvKm2mhucuF0X-kO5jVhttps://goo.gl/8LKttJ For complete video course click here: https://goo.gl/8LKttJ https://www.youtube.com/watch?v=yNnGavnlTZ0&list=PL9UP_4zHScPweZMvKm2mhucuF0X-kO5jV … [Read more...]
Exploring PKI and Asymmetric Encryption
Exploring PKI and Asymmetric Encryption Understanding Asymmetric Algorithms Asymmetric algorithms support two of the primary objectives of any form of security, because their main objectives are confidentiality and authentication. To meet these objectives, these algorithms are based on much more complex mathematical formulas that require greater time to compute than symmetric … [Read more...]
Implementing Digital Signatures
Implementing Digital Signatures Examining Hash Algorithms For centuries everyone from kings to generals to college students has wanted to ensure the authenticity of their communications. In this section we will examine the role of hash algorithms in helping provide this assurance through the process of hashing. Along the way we will examine hash functions and learn about … [Read more...]