Providing SAN Security
Overview of SAN Operations
Organizations are producing ever-increasing amounts of data. A storage-area network (SAN) is an effective means to allow them to store and access this data in a secure fashion. This section examines the fundamentals of SAN operation and describes the technology behind these focused networks. It also examines attacks focused on SANs and discusses their defense.
Fundamentals of SANs
With ever-increasing storage needs, many organizations are moving away from traditional file servers to more sophisticated SAN solutions that are made up of a specialized network that enables fast, reliable access among servers and external storage resources. No longer is the storage device the exclusive property of a given server; instead, in a SAN solution, storage devices are shared among all networked servers as peer resources. In much the same way that a LAN is used to connect clients to servers, a SAN may be used to connect servers to storage, servers to each other, and storage to storage. Figure 8-1 shows a SAN in a basic network topology.

A SAN doesn’t need to be a physically separate network. The SAN can be implemented on a dedicated subnet built to carry only business-critical I/O traffic between servers and storage devices. The subnet where the SAN resides would not be burdened with
general-purpose traffic such as e-mail or database access. Instead, it would be limited to I/ O traffic, such as reading a file from a disk or writing a file to a disk.
Traditional LANs with file servers suffer performance hits as they share the network with general network traffic. Taking the approach described here allows you to increase efficiency and drive down access time for clients. These areas are compromised when you use a single network for all applications.
Organizational Benefits of SAN Usage
Whenever a network or server is unavailable, companies suffer a loss both in terms of productivity and potentially in revenue. This makes it critical that data storage be highly available. At the same time, the amount of data that needs to be managed and stored is increasing significantly each year.
Compared to traditional file server solutions, SANs offer an effective means to deal with this ever-increasing amount of data, while helping ensure its ongoing availability. An added benefit of implementing a SAN is that you can offload storage-related data traffic from your daily network operations. By establishing a direct connection between your storage media and servers, you see an increase in performance as well. For many organizations, incorporating SANs in their enterprise infrastructure allows them to meet three primary business requirements:
- Effectively meet changing business priorities, application requirements, and revenue growth
- Increase performance of long-distance replication, backup, and recovery to meet regulatory requirements as well as industry best practices
- Decrease both capital and operating expenses associated with data storage
Cisco offers an enterprise-wide approach to deploying scalable, highly available, and more easily administered SANs to meet these requirements for the enterprise. Figure 8-2 shows SAN usage in the enterprise.

Cisco offers solutions for intelligent SANs that are designed to be an integral part of an enterprise data center architecture. This provides a better way to access, manage, and protect growing information resources. The Cisco SAN solution provides access across a consolidated Fibre Channel, Fibre Channel over IP (FCIP), Internet Small Computer Systems Interface (iSCSI), Gigabit Ethernet, or optical network for improved performance and access.
Understanding SAN Basics
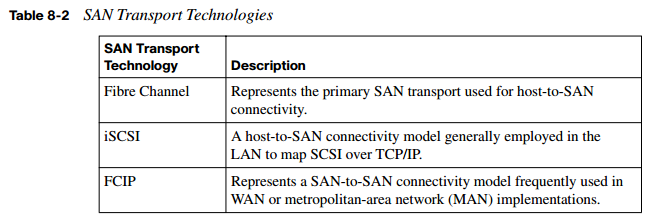
The Small Computer Systems Interface (SCSI) communications model serves as the basis for all the major SAN transport technologies. In fact, many might say that a SAN can best be described as the merging of SCSI and networking. This combination makes for the fast, reliable data access and storage that today’s enterprise networks need. Table 8-2 describes the three major SAN transport technologies.
Fundamentals of SAN Security
With more and more critical data created each business day, and that data now residing on a SAN, security is a top concern. Securing your SAN solution calls on the processes and solution features that protect the integrity and availability of data stored on storage networks. Providing a comprehensive SAN security solution involves four key aspects:
- Centralized authentication, authorization, and logging of all changes via secure rolesbased management
- Centralized authentication of devices connected to the network, ensuring that only authorized devices may be connected
- Secure transmission and receipt of data through traffic isolation and access controls, which ensure protection from activities of other devices in the network
- Full encryption of all data leaving the storage network for business continuance, remote vaulting, and backup. Figure 8-3 shows aspects of SAN security.

The Cisco MDS 9000 family of products is designed to allow storage professionals to achieve optimal security for their SANs. The security features of this product line make it well suited for data-critical environments that require the highest levels of security, such as government, banking, and patient records in healthcare environments.
The MDS 9000 SAN-OS from Cisco provides a comprehensive approach to network security. In addition to providing services such as virtual storage-area networks (VSAN), aimed at providing true isolation of SAN-attached devices, Cisco’s SAN-OS offers a myriad of additional security features to provide secure local and remote SAN deployments. These features include such things as switch and host authentication using Fibre Channel Security Protocol (FC-SP), IP security for FCIP and iSCSI, role-based access control, port security and fabric binding, and zoning.
Classes of SAN Attacks
As with other areas of your LAN, your SAN is not immune to attacks. There are several types of attacks against SANs. In general, they all fall into one of three classes of attack, as shown in Table 8-3.

Implementing SAN Security Techniques
With the ever-increasing importance of data storage in enterprise environments, we must also be concerned about securing this data—as it resides on the disk and when it is in transit on the network. This section explores a number of technologies you can use to secure your SAN environment to better protect your valuable data.
Using LUN Masking to Defend Against Attacks
A Logical Unit Number (LUN) is an address for an individual disk drive and, by extension, the disk device itself. The SCSI protocol uses the term LUN as a way to differentiate the individual disk drives that comprise a common SCSI target device, such as a SCSI disk array.
To defend against attacks, LUN masking may be employed. In this authorization process, a LUN is made available to some hosts and unavailable to other hosts. Generally, this technique of LUN masking is implemented at the host bus adapter (HBA) level. Unfortunately, when LUN masking is implemented at this level, it is vulnerable to any attack that compromises the HBA.
Benefits, with regard to security, are limited with the implementation of LUN masking. This is because with many HBAs it is possible for an attacker to forge source addresses. For this reason, LUN masking is implemented mainly as a way to protect against malfunctioning servers corrupting disks belonging to other servers.
An example of where LUN masking might be useful is in the case of Windows servers attached to a SAN. In some instances these corrupt non-Windows volumes by attempting to write Windows volume labels to them. In these cases, hiding the LUNs of the nonWindows volumes from the Windows server can prevent this behavior. With the LUNs masked, the Windows server is unaware of the non-Windows volumes and thereby makes no attempt to write Windows volume labels to them. In today’s implementations, typically LUNs are not individual disk drives but rather virtual partitions (or volumes) within a RAID array.
Examining SAN Zoning Strategies
It is not uncommon for a SAN to contain a number of different storage devices. In these instances, for security purposes, one device should not necessarily be allowed to interact with all other devices in the SAN. To prevent this behavior, Fibre Channel zoning may be employed. Fibre Channel zoning is the partitioning of a Fibre Channel fabric into smaller subsets. Figure 8-4 shows an example of Fibre Channel zoning.

Examining Soft and Hard Zoning
Although both zoning and LUN masking have the same objectives, zoning is implemented on fabric switches, and LUN masking is performed on endpoint devices. Because zoning is implemented at the switch level, rather than on the individual endpoints, when compared with LUN masking, zoning may also be a more secure measure. The Cisco MDS 9100 series fabric switch, shown in Figure 8-5, represents a cost-effective, intelligent SAN solution that allows for the implementation of zoning.

The two main zoning methods are hard zoning and soft zoning. With soft zoning, you restrict only the fabric name services. In other words, soft zoning shows a device only an allowed subset of devices. So, with soft zoning in place, when a server looks at the fabric’s content, it sees only the devices it is allowed to see. However, this does not prevent the fact that any server can attempt to contact other devices based on their addresses.
Compared to soft zoning, hard zoning truly restricts communication across a fabric by using access control lists (ACL) that are applied by the switch port ASIC to every Fibre Channel frame that is switched. This approach is more secure than soft zoning and is more commonly used. Whether you choose to apply hard or soft zoning, be aware that these security measures apply only to the switched fabric topology.
Understanding World Wide Names
Fibre Channel networks use 64-bit addresses known as World Wide Names (WWN) to uniquely identify each element in a Fibre Channel network. These WWNs may be used in zoning to assign security permissions. Figure 8-6 shows a Cisco MDS 9100 series switch with a sample WWN assigned.

Name servers in the switches may also be used to either allow or block access to particular WWNs in the fabric. However, using WWNs for security purposes is inadvisable. WWNs are inherently insecure because a device’s WWN is a user-configurable parameter. Using WWNs for zoning is susceptible to unauthorized access, because the zone can be bypassed through an attacker spoofing the WWN of an authorized HBA.
Defining Virtual SANs
In addition to traditional SANs, you may create a virtual storage-area network (VSAN). VSANs were originally invented by Cisco, but they are now an ANSI standard. Figure 8-7 shows the construction of a VSAN.

A VSAN is created from a collection of ports that are part of a set of connected Fibre Channel switches. These ports together form a virtual fabric. Ports within a single switch can be partitioned to form multiple VSANs if you like. Conversely, you can use multiple switches together and join any number of their ports to form a single VSAN. If this sounds familiar, VSANs when put together in this manner strongly resemble VLANs. Like
VLANs, all traffic is tagged as it crosses interswitch links with the VSAN ID. Another commonality with VLANs is that through the construction of VSANs we can add a layer of security at the port level.
Combining VSANs and Zones
Combining VSANs and zones is an effective means of providing security control for your VSAN. To combine these complementary protocols, you first must associate the physical ports with a VSAN. This step is quite similar to associating switch ports with VLANs. Next you need to logically divide the VSANs into zones. With these actions complete, you can effectively provide a security control for your VSAN. Figure 8-8 shows how VSANs work with zones.

Identifying Port Authentication Protocols
You need to be aware of two primary port authentication protocols when working with VSANs:
- Diffie-Hellman Challenge Handshake Authentication Protocol (DHCHAP)
- Challenge Handshake Authentication Protocol (CHAP)
Understanding DHCHAP
DHCHAP may be used to authenticate devices connecting to a Fibre Channel switch. By using Fibre Channel authentication, you allow only trusted devices to be added to a fabric. This prevents unauthorized devices from accessing the Fibre Channel switch.
DHCHAP supports both switch-to-switch and host-to-switch authentication. It’s a mandatory password-based, key-exchange authentication protocol. Before any authentication may be performed, DHCHAP negotiates hash algorithms and DiffieHellman (DH) groups. In addition, it supports Message Digest 5 (MD5) and Secure Hash Algorithm 1 (SHA-1)-based authentication.
CHAP in Securing SAN Devices
CHAP is the mandatory protocol for iSCCI, as chosen by the Internet Engineering Task Force (IETF). CHAP has been around for quite some time and is based on shared secrets. To strengthen CHAP, DHCHAP adds a DH exchange that both strengthens CHAP and provides an agreed-upon secret key. The goal of DHCHAP is to be a simple, easy-toimplement protocol.
Working with Fibre Channel Authentication Protocol
If your organization needs a stronger means of securing the SAN than the password-based mechanism used in CHAP, Fibre Channel Authentication Protocol (FCAP) is available. FCAP, shown in Figure 8-9, was born from Switch Link Authentication Protocol (SLAP), the first authentication protocol proposed for Fibre Channel. With changes over time, this protocol was generalized and renamed FCAP. This optional authentication mechanism may be employed between any two devices or entities on a Fibre Channel network. It uses certificates or optional keys to provide a stronger level of security.

FCAP relies on an underlying public key infrastructure (PKI) to provide enterprise-class security. By using PKI, often present in more security-conscious organizations, as a foundational element, along with a certificate-based protocol, FCAP provides numerous advantages. Central among these are strong authentication and management data integrity. For some organizations, the complexities associated with a PKI can be daunting. This is the only significant argument against FCAP.
Understanding Fibre Channel Password Authentication Protocol
Fibre Channel Password Authentication Protocol (FCPAP) is an optional password-based authentication key-exchange protocol. It may be used in Fibre Channel networks to provide mutual authentication between Fibre Channel ports. FCPAP, which is based on passwords, was proposed as an alternative to FCAP. It has its roots in another protocol called Secure Remote Password (SRP).
As compared to FCAP, FCPAP does not require a PKI to operate. This was one of the main drivers behind its proposal. Although FCPAP does not require PKI, complexities are still associated with managing the passwords and other aspects of FCPAP.
Assuring Data Confidentiality in SANs
SANs provide an effective way for organizations to meet the ever-expanding need to store data. Because organizations store everything from social security records to client records to proprietary information on SANs, it is extremely important that this storage medium be secure and that the data be secure while in transit. This section examines the benefits of incorporating Encapsulating Security Payload (ESP) in your SAN solution. As an Internet standard, ESP can provide both encryption and authentication to further secure an organization’s crucial data. We will also discuss the use of Fibre Channel Security Protocol
(FC-SP) to provide both host-to-switch and switch-to-switch authentication to further secure enterprise-wide fabrics.
Incorporating Encapsulating Security Payload (ESP)
SANs are designed to provide fast access and expandable storage for your data needs. However, that access must also be secure. ESP represents a means of providing this security. ESP is an Internet standard that allows IP packets to be authenticated and encrypted.
ESP is a common security standard in many IP networks, but it also has been adapted for use in Fibre Channel networks. In fact, the IETF iSCSI proposal specifies ESP link authentication and optional encryption. ESP over Fibre Channel provides a means of protecting data in transit throughout the Fibre Channel network. Although ESP over Fibre Channel is an effective means to secure data while it is in transit, it does not address the need to secure data while it is stored on the Fibre Channel network.
Providing Security with Fibre Channel Security Protocol
FC-SP is designed to overcome the security challenges for enterprise-wide fabrics by providing switch-to-switch and host-to-switch authentication. FC-SP is a project of Technical Committee T11 of the International Committee for Information Technology Standards (INCITS). It focuses on protecting data in transit throughout the Fibre Channel network. Much like ESP, FC-SP does not address the security of data stored on the Fibre Channel network.
FC-SP is a security framework that includes a number of protocols to enhance Fibre Channel security in several areas. For instance, FC-SP addresses the authentication of Fibre Channel devices. It also provides cryptographically secure key exchange and cryptographically secure communication between Fibre Channel devices.