Exploring Voice Security
Given that VoIP is another application that uses an IP network, it is also fair to say that many of the best practices that we have discussed in previous chapters will be employed in securing a VoIP network. Before we look at methods of securing a VoIP network, we first look at some basic VoIP terminology. Only then can we examine specific vulnerabilities and the possible exploits that might be leveraged against those vulnerabilities.
VoIP Components
In order to understand VoIP security, you should first understand these basic VoIP components and concepts:
- IP Phones. Responsible for delivering voice over IP to the desktop.
- Gatekeeper. Like a traffic cop on a VoIP network. Provides Call Admission Control (CAC), bandwidth management and control, and network address translation.
- Gateway. Translates VoIP to PSTN and vice versa. A gateway also represents a physical connection point for an organization’s local analog and digital voice devices (phones, fax machines, and so on) and Private Branch Exchanges (PBXs).
- Multipoint Control Unit (MCU). Allows multiple participants in different locations to connect to the same conference call or video conference.
- Call Agent. Similar to a proxy, acts as an agent for controlling IP phones, CAC (see Gatekeeper above), bandwidth management and control, and network address translation. Cisco Unified Communications Manager (UCM) and Unified Communications Manager Business Edition serve as call agents.
- Application Servers. These provide extra services such as unified messaging and voice mail. Cisco Unity is an application server.
- Videoconference Station. Provides an interface to videoconferencing services for an end user. The stations have a camera for video input capture and a microphone for audio, as well as screens and speakers to provide two-way videoconferencing with a remote user.
Common VoIP Protocols
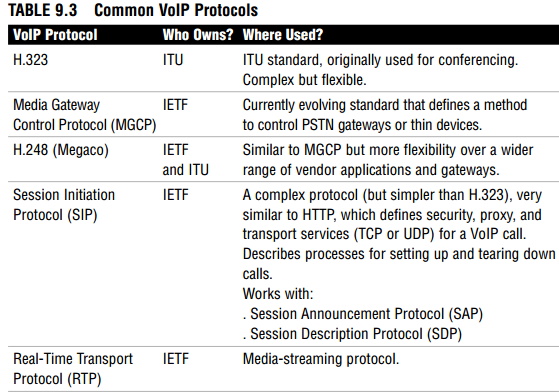
Table 9.3 lists and defines some common VoIP protocols.
Memorize these terms, as they will likely be on the exam. Also, although all of these VoIP protocols have their own specific vulnerabilities, SIP has such a large (and growing) installed base that Cisco has chosen SIP alone as an example to analyze shortly in the subsection, “SIP Vulnerabilities.”
Threats to VoIP Endpoints
Regardless of the VoIP protocol chosen, there are common threats to a VoIP network:
- Reconnaissance. Using commonly known reconnaissance techniques to discover the protocols that are being used for the VoIP implementation.
- Spam over IP Telephony (SPIT). Not a problem yet, but the fact that we are talking about it means that it might be a future threat. Traditional anti-spam measures (such as IronPort) will not be effective in dealing with this threat. That said, simple measures, such as implementing authentication and TLS (Transport Layer Security), would be effective tools to mitigate its threat.
- DoS Attacks. These fall into three general categories:
- Network resource overload. Most commonly uses bandwidth overloading to make a network resource such as a VoIP phone or a call agent unavailable.
- Host resource starvation. Using up host resources such that the host can no longer serve legitimate connection requests. A SYN flood is a good example.
- Out-of-bounds attacks. The process of creating anomalous data packets with unexpected data that is outside the scope (or bounds) causing system crashes.
- Eavesdropping. The unauthorized interception of RTP media streams of VoIP packets for the purpose of accessing confidential information. Can be mitigated simply by using encryption.
- Man-in-the-Middle Attacks. Common man-in-the middle attacks such as those discussed in Chapter 1, “Network Insecurity,” could prove to be effective.
Fraud
The two most common forms of fraud on VoIP networks are the following:
- Vishing. Phishing a VoIP network to attempt to compromise confidentiality.
- Theft and Toll Fraud. Fraudulently using VoIP services that do not belong to you.
These Cisco Unified Communications Manager (UCM) features can protect the VoIP network against fraud: - Partitioning. Limit phone access to only certain parts of the dial plan.
- Dial Plans. Filter possibly exploitive phone numbers.
- Forced Authorization Codes (FACs). A feature in UCM that can track calls and prevent unauthorized calls in the first place.
SIP Vulnerabilities
As mentioned, all VoIP protocols have specific vulnerabilities. SIP is a good example of a protocol whose design did not include security, and as such is a poster child for examining securing VoIP protocols. SIP has very little integral security. It is a relatively immature protocol that is nevertheless seeing widespread adoption. There are three main vulnerabilities with the protocol, as follows:
- Registration Hacking. Hackers can intercept incoming calls and spoof the registration server, thus rerouting the calls through themselves. This is similar to an ICMP redirect (see Chapter 1).
- Message Tampering. Because the VoIP messages are carried in cleartext, it is relatively simple for a hacker to alter the VoIP packet contents traveling between SIP endpoints.
- Session Tear-Down. Allows a hacker to prematurely tear down an existing VoIP session. Similar to an RST attack employed in many IP DoS attacks.
These three main vulnerabilities can be mitigated using the techniques and technologies discussed in the next section, “Mitigating VoIP Hacking.”
Mitigating VoIP Hacking
Although we have only (and briefly) examined specific SIP vulnerabilities, the following techniques can be used to secure any VoIP infrastructure regardless of the protocol employed and will be examined separately:
- Voice VLANs (VVLANs)
- Firewalls
- VPNs
- Correct VoIP Endpoint Configuration
- Correct VoIP Server Configuration
Voice VLANs (VVLANs)
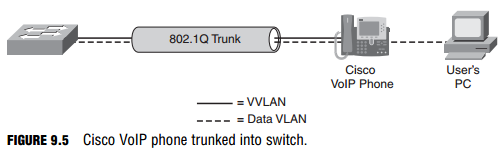
Recall the concept of separating traffic into different planes. For example, the data plane should be kept separate from the management plane whenever possible. This same discussion holds true for VoIP too. If the VoIP traffic can be separated into a VLAN separate from the data VLAN, it would be much more difficult for a hacker to use a Man-in-the-Middle (MiM) attack or similar to eavesdrop, tamper with, or reconnoiter the VoIP traffic. Figure 9.5 illustrates using separate VLANs for voice and data. A VoIP phone is connected via an IEEE 802.1Q trunk to a Cisco Catalyst switch. A user’s PC is connected to the
VoIP phone via the supplied data jack. The switch port in which the VoIP phone is connected is set to trust the VoIP phone’s tagging of its own Ethernet frames with the VLAN number of the Voice VLAN (VVLAN). Other frames, such as those from the PC connected to the VoIP phone, will be tagged for the data VLAN, keeping the data and voice planes separate. This has the further advantage of making Quality of Service (QoS) possible for the VoIP traffic because the VLAN tag makes it simple to identify and allows the QoS-aware switch to apply differentiated, possibly preferential, treatment to the VoIP traffic.
Protect VoIP Networks with Firewalls
Firewalls such as the Cisco Adaptive Security Appliance (ASA) 5500 Series are an integral part in an overall VoIP security policy. Here are some of the features
of Cisco firewalls that you can leverage on in order to increase the security of the VoIP implementation and mitigate some of the common threats that were previously outlined:
- Standards Compliance. Ensure that VoIP protocols are standard-compliant and that only SIP methods are sent to UCM.
- Rate Limiting. Rate limit SIP requests to prevent DoS attacks.
- Enforce Call Policies. Create an acceptable use policy of white lists, black lists, SIP URIs, and matching called/caller parties and enforce it.
- Inspection. Firewall dynamically opens TCP and UDP ports for Cisco applications by inspecting the VoIP sessions for this embedded information. Also enable the inspection of encrypted phone calls by the firewall.
- Registration. Permit only registered phones to make calls.
Protect VoIP Networks with VPNs
As we saw in Chapter 7, “Virtual Private Networks with IPsec,” VPNs seem to be the magic bullet for many issues where network confidentiality, integrity, and authentication are required. For example, an IPsec VPN could be constructed for VoIP-only traffic between two IOS routers acting as gateways. To accomplish this, an ACL specifying which protocols, addresses, port numbers, and so on will be necessary to properly differentiate the VoIP traffic from other site-to-site flows. The use of ACLs and their application to an IPsec crypto map were discussed in Chapter 7. The ACLs that we used in Chapter 7 were not very granular, in that they specified site-to-site flows based solely on IP addresses. These were essentially layer 3-only filters. There are some drawbacks to using an IPsec VPN solution for VoIP, though. Cisco points out that the more specific filtering for which traffic should be transported inside an IPsec VPN (such as would be needed for VoIP flows) should only be used if necessary, because this more granular filtering is more CPU-intensive.
Another caveat in using IPsec VPNs with VoIP is in the area of quality of service (QoS). The VoIP endpoint or server will definitely map the bits in the ToS (Type of Service) byte of the IP header in attempt to express its requirement for QoS on the network. This process is called marking. The IPsec VPN solution must find a way to map these bits into the unencrypted IP packet header, such that QoS-aware devices that are intermediate to the VoIP devices can properly honor the QoS marking of VoIP systems, and thus preserve end-to-end QoS in the network, even over the VPN.
Be careful when you implement VoIP inside a VPN across a large public network such as the Internet. QoS is impossible to maintain end-to-end over the Internet because we have no control over the routers that will be forwarding the packets. This makes VoIP over the Internet somewhat problematic since QoS is traditionally a big issue with VoIP in general. An optimum solution would be a VPN constructed over a service provider’s network where the service provider is required to maintain a certain level of service as stipulated in a service level agreement (SLA)
Protect VoIP Networks with Correct Endpoint Configuration
Careful configuration of the VoIP telephone endpoints will go a long way to
creating a secure VoIP network. Password protecting or disabling the ability to configure the device altogether by the user is a good first step. The following are other things you may consider:
- Firmware. Make sure that only firmware digitally signed by the manufacturer is installed on the devices. (Digital signatures and HMACs are covered in Chapter 6, “Introducing Cryptographic Services.”)
- Configuration files. Use only signed configuration files.
- Disable unnecessary features. Disable the following features if they are not needed. (Remember the principle of least privileges.):
- PC port
- Setting button
- Speakerphone
- WWW access
Protect VoIP Networks with Correct Server Configuration
Using a Cisco solution that includes the Unified Communications Manager means that several security features will be built in, as follows:
- File system and OS applications are inaccessible.
- Only images digitally signed by Cisco are installable.
- The device follows best practices for hardening including:
- Unused services are removed, and defaults such as usernames are disabled.
- UCM is constantly improved over time as new threats are discovered.
- UCM logs security events.
- CSA is enabled on UCM by default.