CCNP Switch FAQ: Switch Operation
Q1. Which of the following devices performs transparent bridging?
a. Ethernet hub
b. Layer 2 switch
c. Layer 3 switch
d. Router
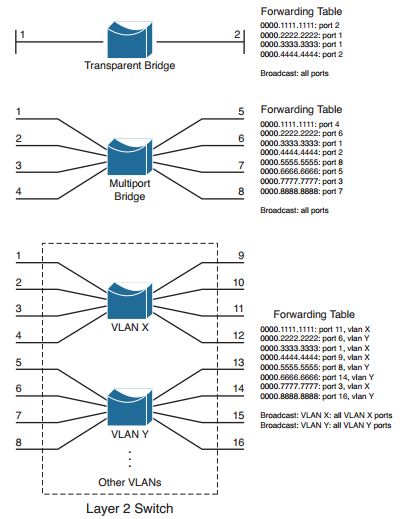
Figure: A Comparison of Transparent Bridges and Switches
Q2. When a PC is connected to a Layer 2 switch port, how far does the collision domain spread?
a. No collision domain exists.
b. One switch port.
c. One VLAN.
d. All ports on the switch.
Q3. What information is used to forward frames in a Layer 2 switch?
a. Source MAC address
b. Destination MAC address
c. Source switch port
d. IP addresses
4. What does a switch do if a MAC address cannot be found in the CAM table?
a. The frame is forwarded to the default port.
b. The switch generates an ARP request for the address.
c. The switch floods the frame out all ports (except the receiving port).
d. The switch drops the frame.
5. In a Catalyst switch, frames can be filtered with access lists for security and QoS purposes. This filtering occurs according to which of the following?
a. Before a CAM table lookup
b. After a CAM table lookup
c. Simultaneously with a CAM table lookup
d. According to how the access lists are configured
6. Access list contents can be merged into which of the following?
a. CAM table
b. TCAM table
c. FIB table
d. ARP table
7. Multilayer switches using CEF are based on which of these techniques?
a. Route caching
b. NetFlow switching
c. Topology-based switching
d. Demand-based switching
8. Which answer describes multilayer switching with CEF?
a. The first packet is routed and then the flow is cached.
b. The switch supervisor CPU forwards each packet.
c. The switching hardware learns station addresses and builds a routing database.
d. A single database of routing information is built for the switching hardware.
9. In a switch, frames are placed in which buffer after forwarding decisions are made?
a. Ingress queues
b. Egress queues
c. CAM table
d. TCAM
10. What size are the mask and pattern fields in a TCAM entry?
a. 64 bits
b. 128 bits
c. 134 bits
d. 168 bits
11. Access list rules are compiled as TCAM entries. When a packet is matched against an access list, in what order are the TCAM entries evaluated?
a. Sequentially in the order of the original access list.
b. Numerically by the access list number.
c. Alphabetically by the access list name.
d. All entries are evaluated in parallel.
12. Which Catalyst IOS command can you use to display the addresses in the CAM table?
a. show cam
b. show mac address-table
c. show mac
d. show cam address-table
More Resources